Getting Started
This knowledge article helps you understand how we're processing compliance, and how it weighs towards your Posture Recommendations score.
Posture Recommendations
This section gives you an at-a-glance overview of the compliance of your Secure checks for your tenants.
To customize your posture checks, please go to: Customize Audit | Customer Knowledge Base (augmentt.com)
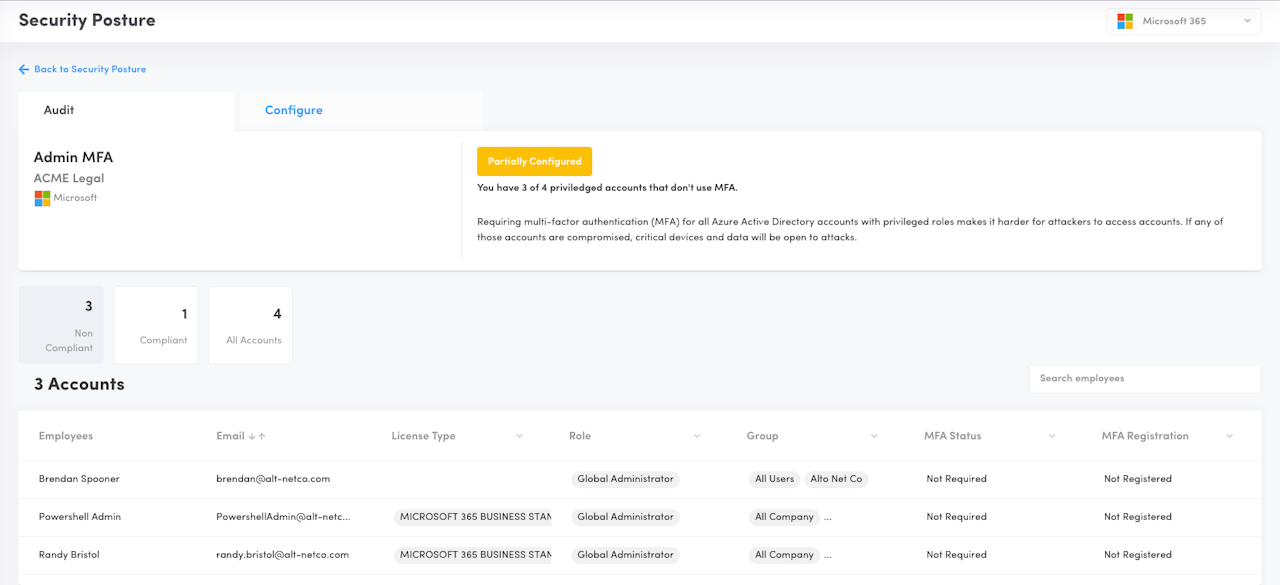
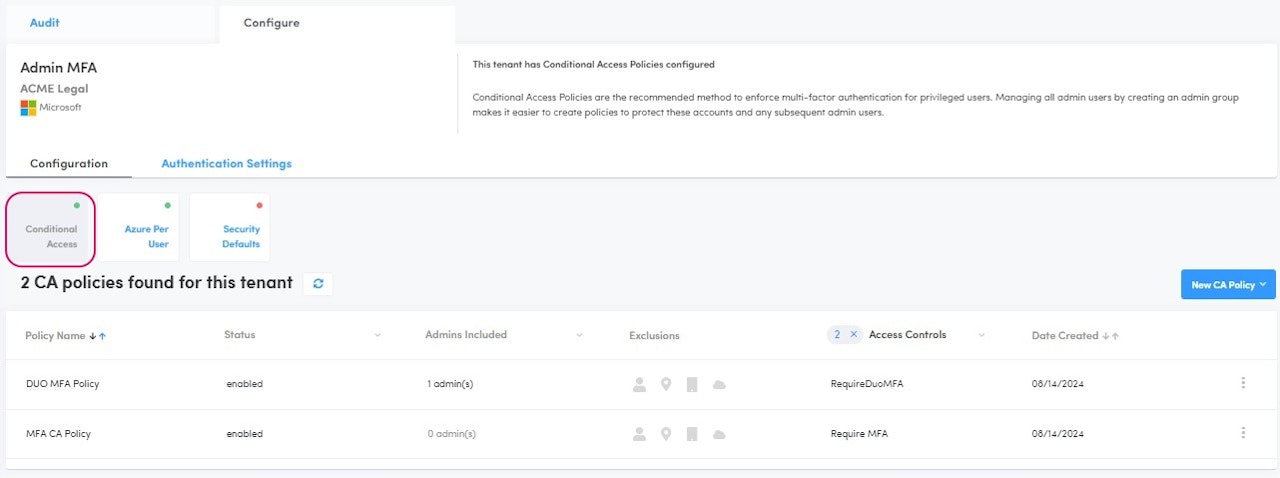
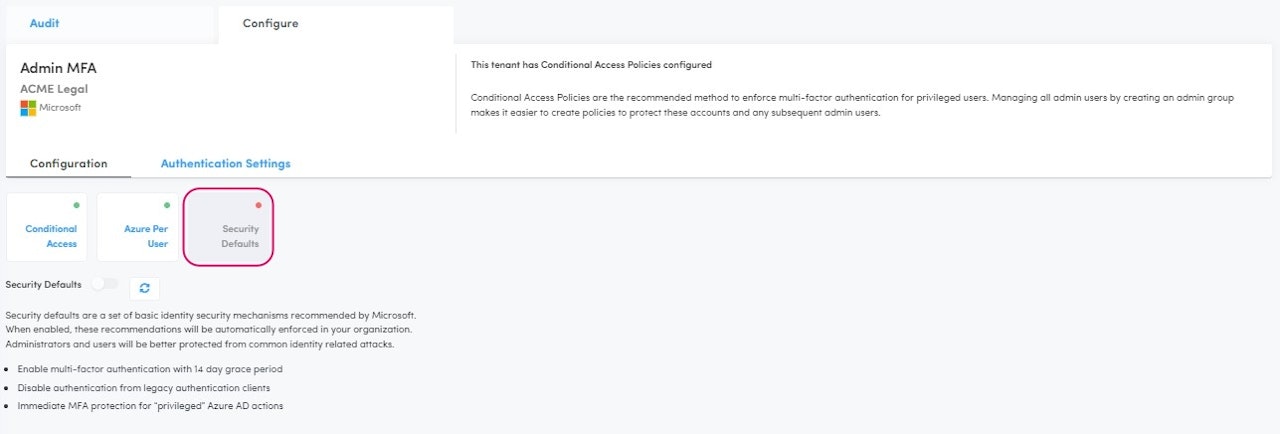
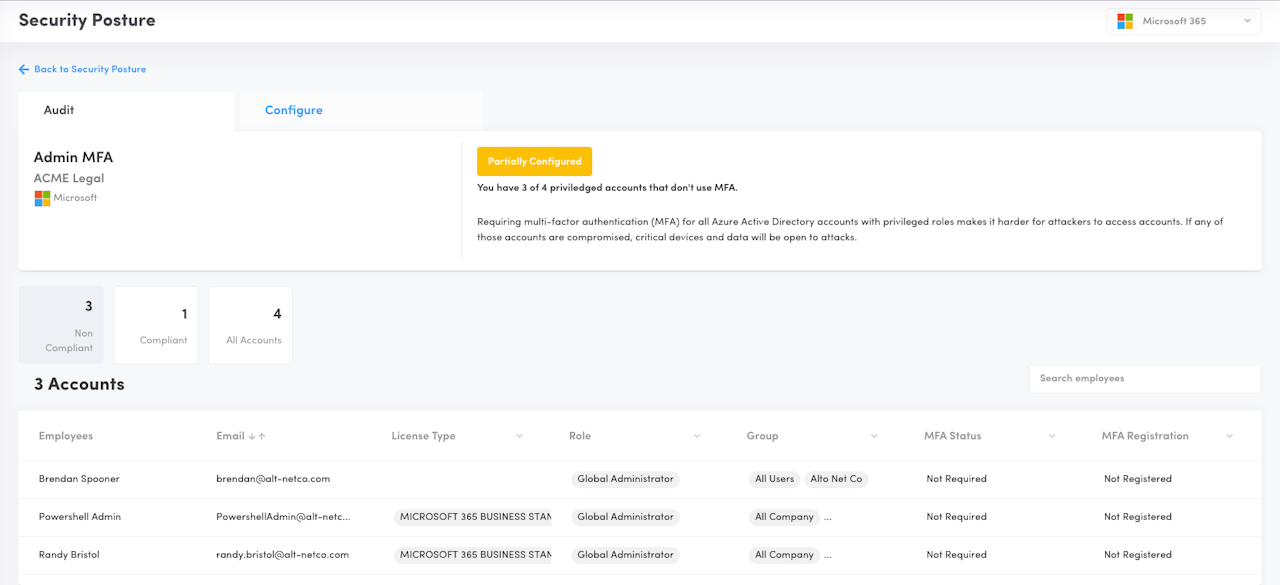
Admin MFA
Description: Verifies all admin accounts MFA requirement, including Security Defaults, Conditional Access Policies or Per-User MFA & DUO in its logic.
Why: Requiring multi-factor authentication (MFA) for all Azure Active Directory accounts with privileged roles makes it harder for attackers to access accounts. If any of those accounts are compromised, critical devices and data will be open to attacks.
How it works:
Security Defaults
If enabled for a tenant, the configuration status will appear as Security Defaults and all users will be considered as Protected. Typically used by tenants that don't have AAD P1 licensing, we are unable to read the MFA registration status of these tenants, the API is behind the AAD P1 paywall. Due to this, we indicate all users as Protected so you, the MSP, can show that your part of the work has been completed by having Security Defaults and hence, MFA enabled.
Legacy (Per User) MFA
This MFA type is being deprecated by Microsoft. Augmentt recommends moving your clients to Security Defaults or Conditional Access before Microsoft fully deprecates this feature.
Conditional Access
Augmentt will read all conditional access policies and identify which ones are applying a grant type of "Require MFA" or "Authentication Strength". The users/groups/roles will be extrapolated from these policies and the related users will be verified for their registration status.
Users having MFA enforcement via Conditional Access and completed successful registration will be considered as protected.
Conditional Access & DUO
Following similar logic to Conditional Access, we will extrapolate policies that have a grant type of "RequireDUOMFA". If the related users have a successful DUO registration and are not in bypassed mode, they will be considered protected.
Non-registered and bypassed users will be Not protected.
Minimum Microsoft Licensing: Works with Basic licensing
Secure Score impact: YES
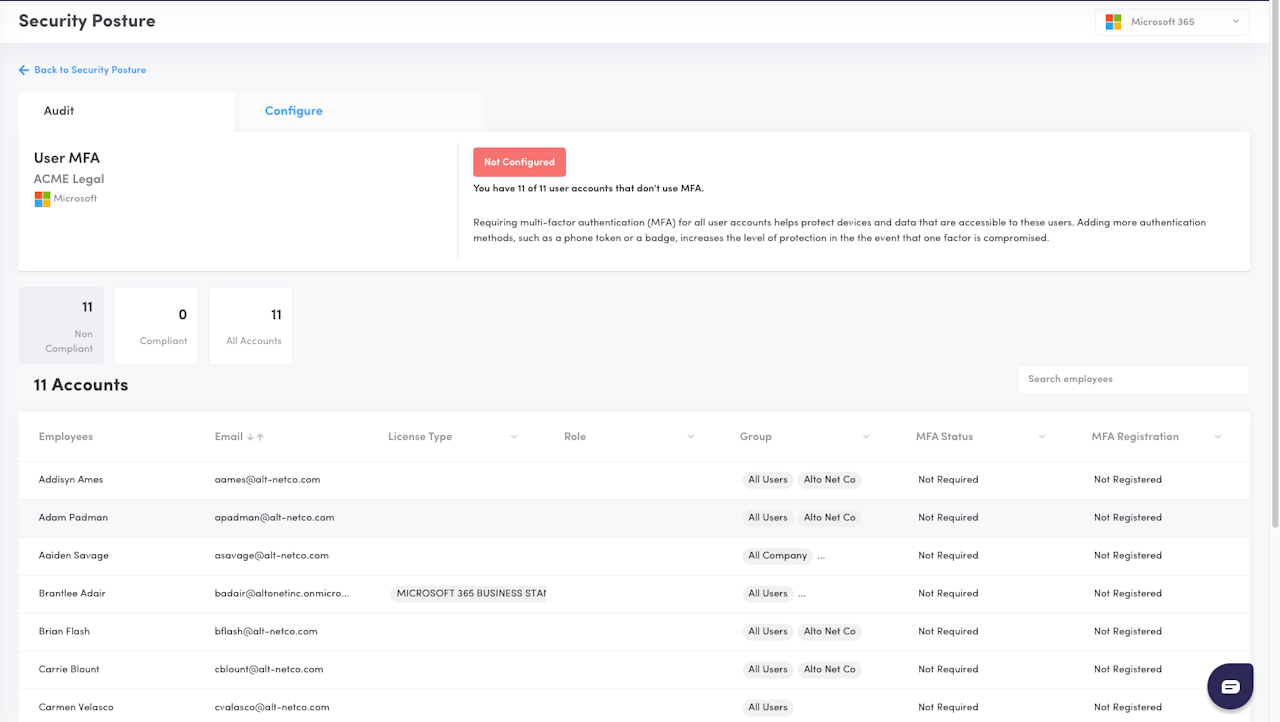
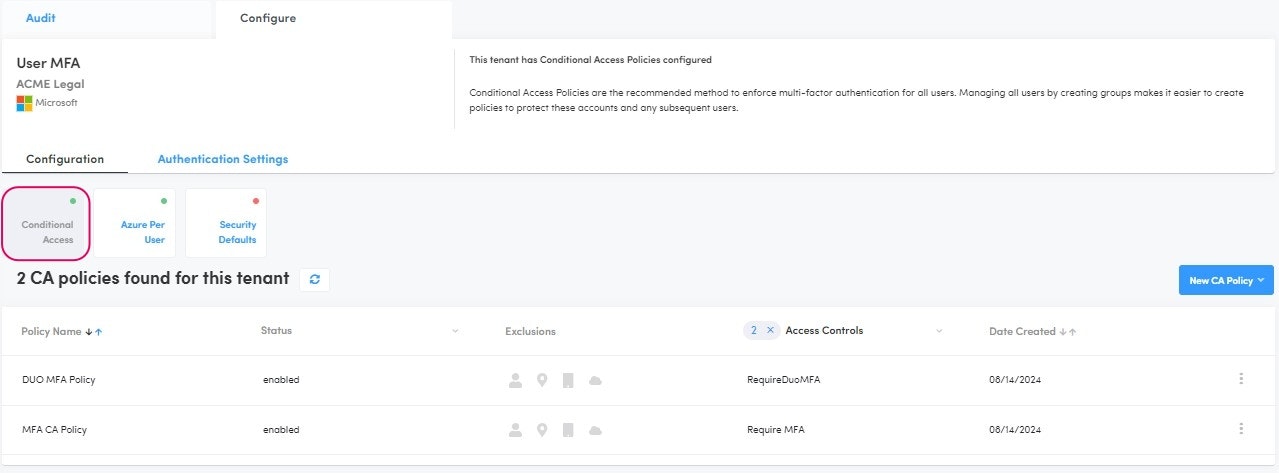
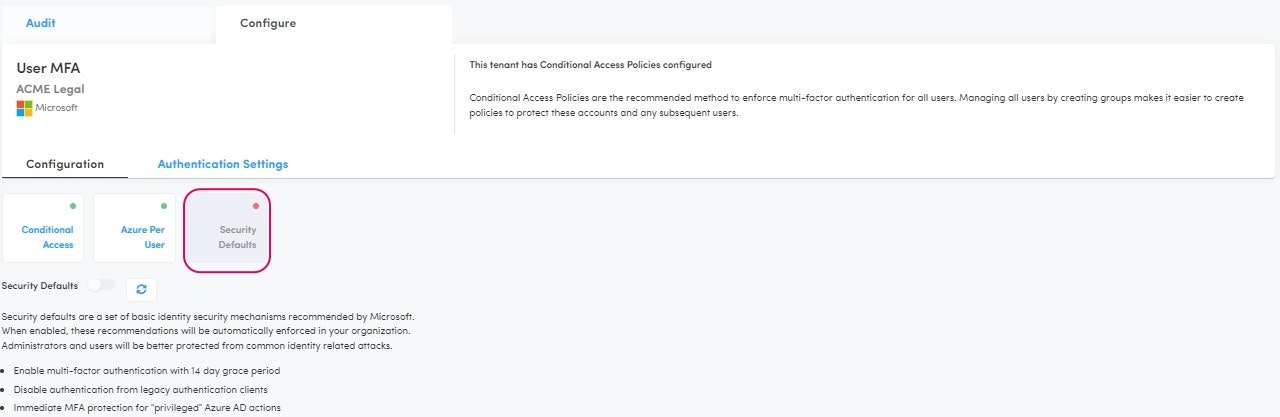
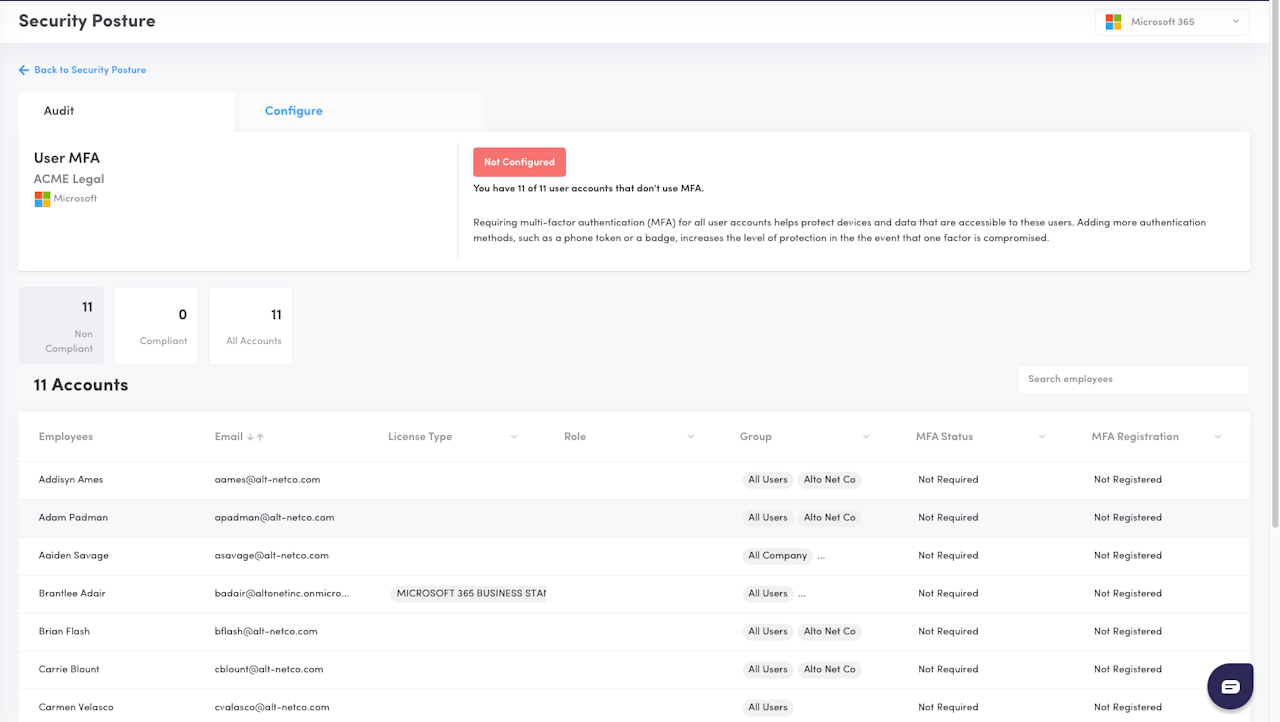
User MFA
Description: Verifies all user (non-admin) accounts MFA requirement, including Security Defaults, Conditional Access Policies or Per-User MFA in its logic.
Why: Requiring multi-factor authentication (MFA) for all user accounts helps protect devices and data that are accessible to these users. Adding more authentication methods, such as a phone token or a badge, increases the level of protection in the the event that one factor is compromised.
How it works:
Security Defaults
If enabled for a tenant, the configuration status will appear as Security Defaults and all users will be considered as Protected. Typically used by tenants that don't have AAD P1 licensing, we are unable to read the MFA registration status of these tenants, the API is behind the AAD P1 paywall. Due to this, we indicate all users as Protected so you, the MSP, can show that your part of the work has been completed by having Security Defaults and hence, MFA enabled.
Legacy (Per User) MFA
This MFA type is being deprecated by Microsoft. Augmentt recommends moving your clients to Security Defaults or Conditional Access before Microsoft fully deprecates this feature.
Conditional Access
Augmentt will read all conditional access policies and identify which ones are applying a grant type of "Require MFA" or "Authentication Strength". The users/groups/roles will be extrapolated from these policies and the related users will be verified for their registration status.
Users having MFA enforcement via Conditional Access and completed successful registration will be considered as protected.
Conditional Access & DUO
Following similar logic to Conditional Access, we will extrapolate policies that have a grant type of "RequireDUOMFA". If the related users have a successful DUO registration and are not in bypassed mode, they will be considered protected.
Non-registered and bypassed users will be Not protected.
Minimum Microsoft Licensing: Works with Basic licensing
Secure Score Impact: YES
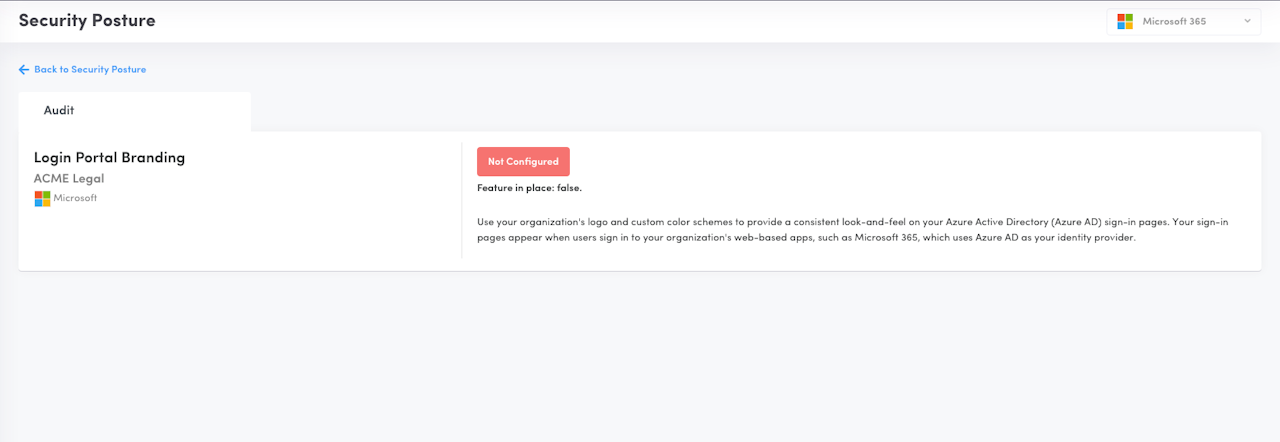
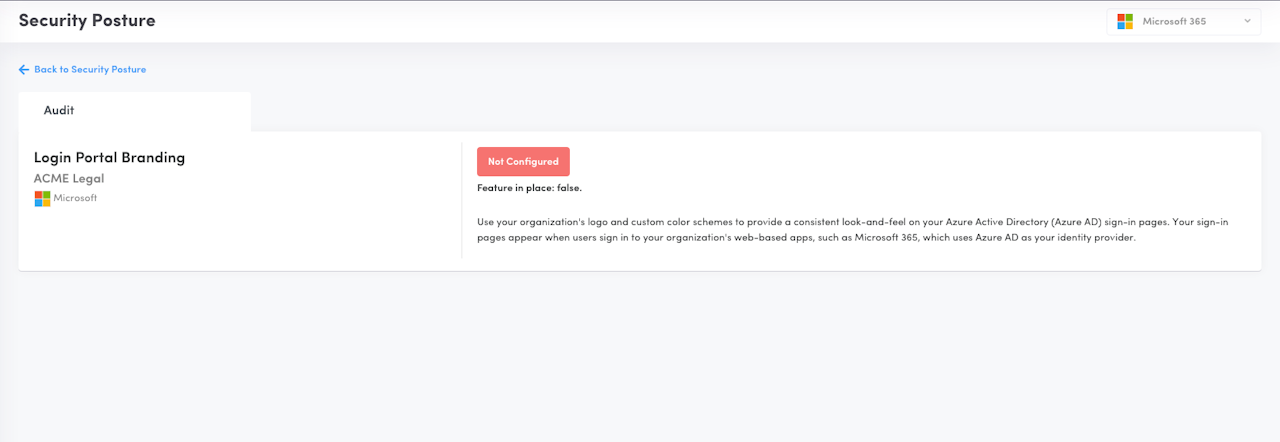
Login Portal Branding
Description: Verifies if Login Portal Logo and Banner are configured
Why: Use your organization's logo and custom color schemes to provide a consistent look-and-feel on your Azure Active Directory (Azure AD) sign-in pages. This allows users to more easily identify fake logins and phishing attempts.
The configurations are applied under Default Sign-In Experience, these are the compliant status in this posture:
Compliant: Both company logo and a custom background image were added.
Partially Compliant: Company logo OR a custom background image added.
Not Compliant: No company logo nor a custom background image added.
Minimum Microsoft Licensing: Works with Basic licensing
Secure Score Impact: No
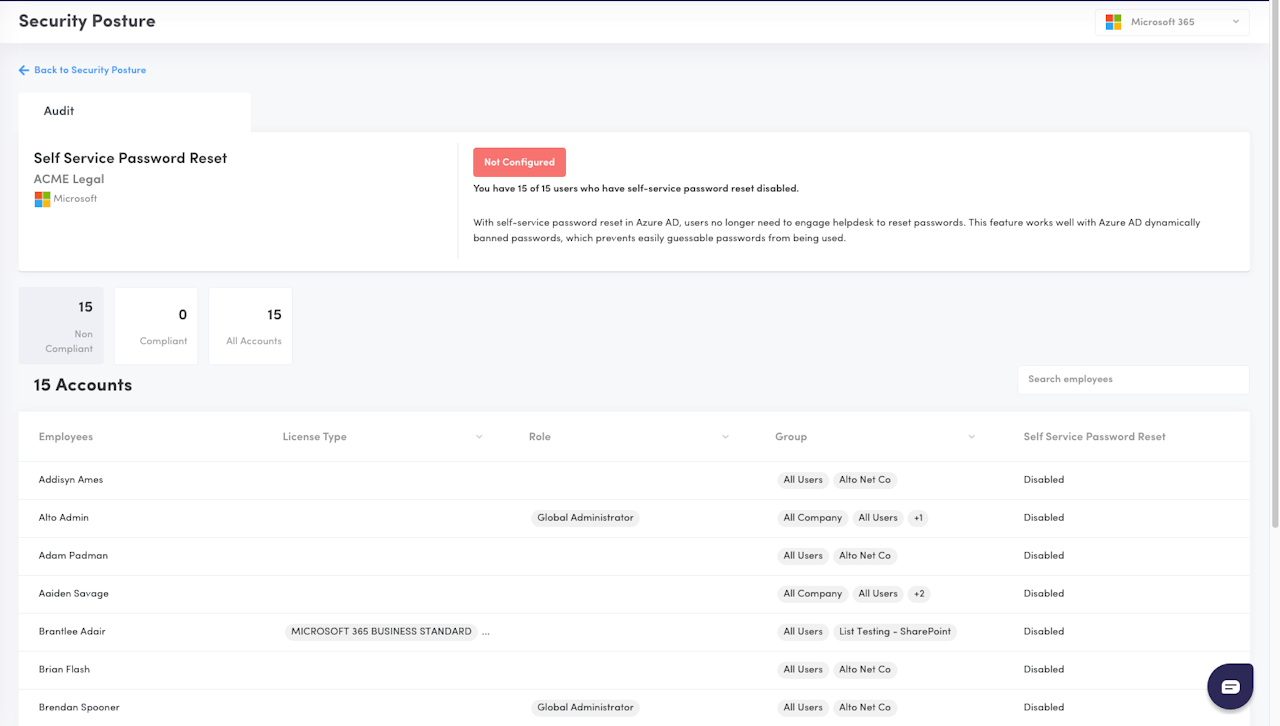
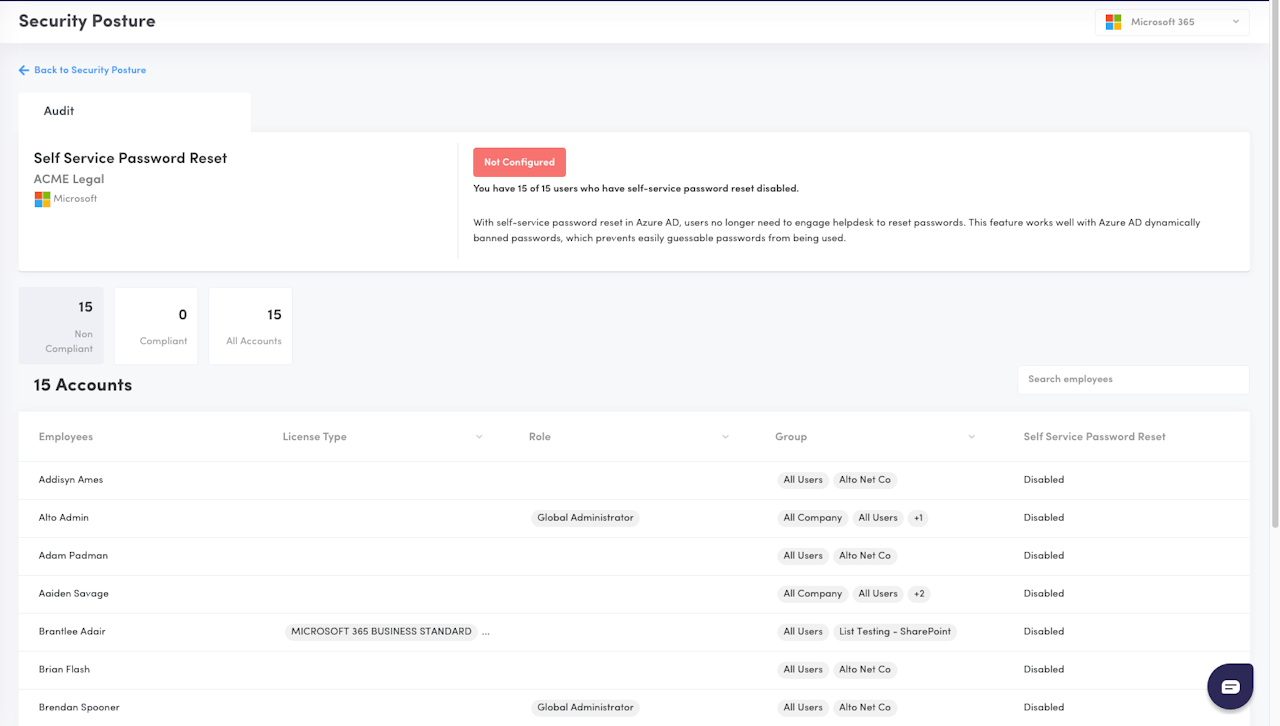
Self Service Password Reset
Description: Verifies if Self Service Password Reset feature is enabled
Why: Enabling Self Service Password Reset (SSPR) in your Microsoft account allows users to reset their passwords without relying on administrators, reducing helpdesk requests and minimizing downtime. This feature also strengthens security by allowing users to change compromised passwords quickly, reducing the likelihood of password-related phishing attacks, and enabling administrators to focus on more critical tasks. By enabling SSPR, administrators can improve user productivity, reduce administrative burdens, and enhance overall security posture.
Minimum Microsoft Licensing: Requires Premium (P1) licensing
Secure Score Impact: YES
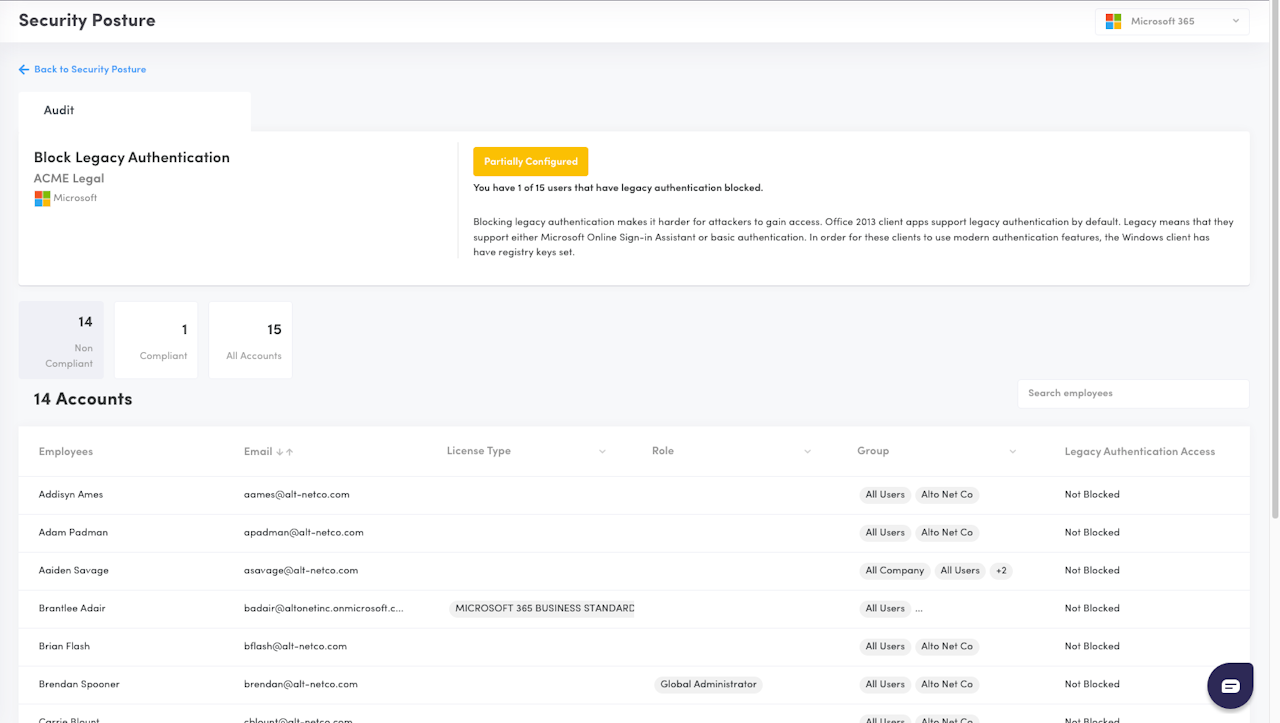
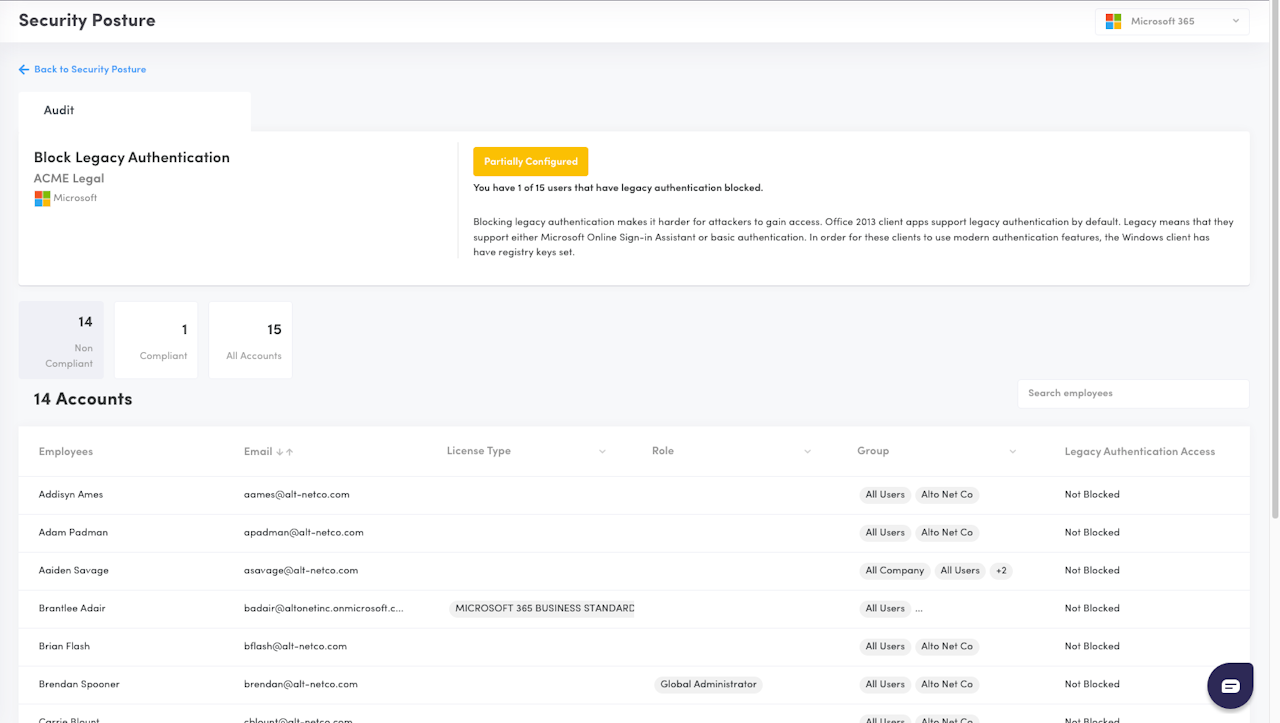
Block Legacy Authentication
Description: Verifies if a Block Legacy Authentication protocol is applied.
Augmentt will locate protocols blocking Legacy Authentication Clients and extrapolate the users of the conditional access policy to determine which users are successfully blocked.
The protocols can be applied via one of the following options:
Organizations with Basic licensing: Blocking via Security Defaults (Security Defaults | Microsoft Learn)
Organizations with Microsoft Entra ID P1 or P2 licenses: Blocking via Conditional Access Policy
Why: Blocking legacy authentication makes it harder for attackers to gain access. Legacy means that they support either Microsoft Online Sign-in Assistant or basic authentication, not supporting MFA.
Minimum Microsoft Licensing: Works with Basic licensing
Secure Score Impact: YES
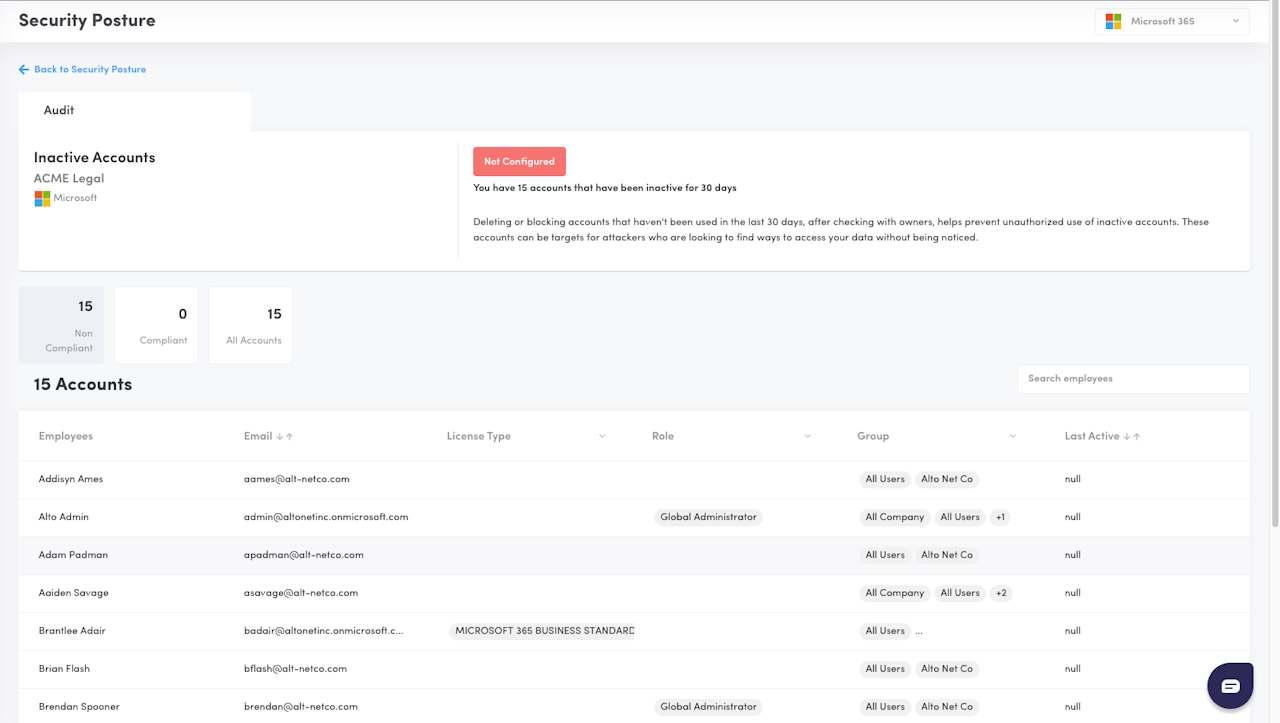
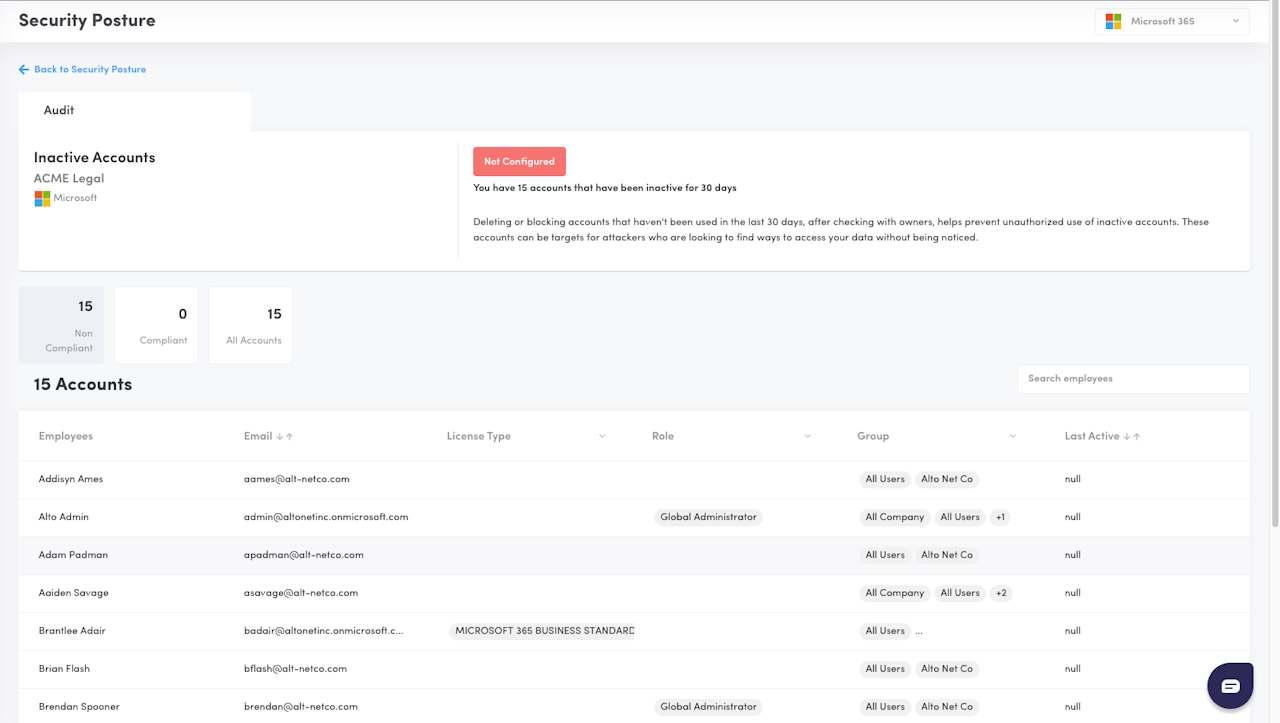
Inactive Accounts
Description: Identifies accounts that have not had any activity for 30 days by looking at the Azure AD sign-in logs as well as the actual app usage of Outlook, Sharepoint, OneDrive and Teams from the Microsoft App Usage Report.
Why: Deleting or blocking accounts that haven't been used in the last 30 days, after checking with owners, helps prevent unauthorized use of inactive accounts. These accounts can be targets for attackers who are looking to find ways to access your data without being noticed.
Configured: 0 accounts are identified as inactive; Scores 1 points
Not Configured: at least 1 account is identified as inactive; Scores 0 points
Microsoft Licensing: Requires Premium (P1) licensing
Secure Score Impact: No
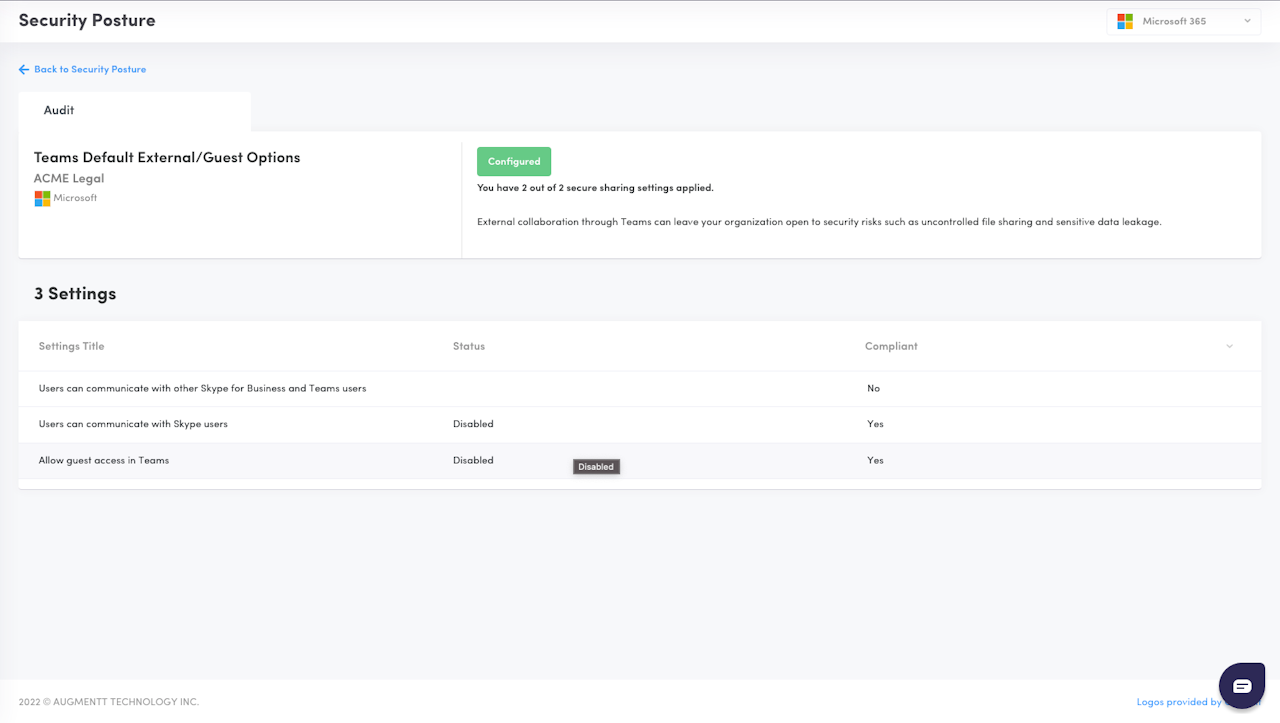
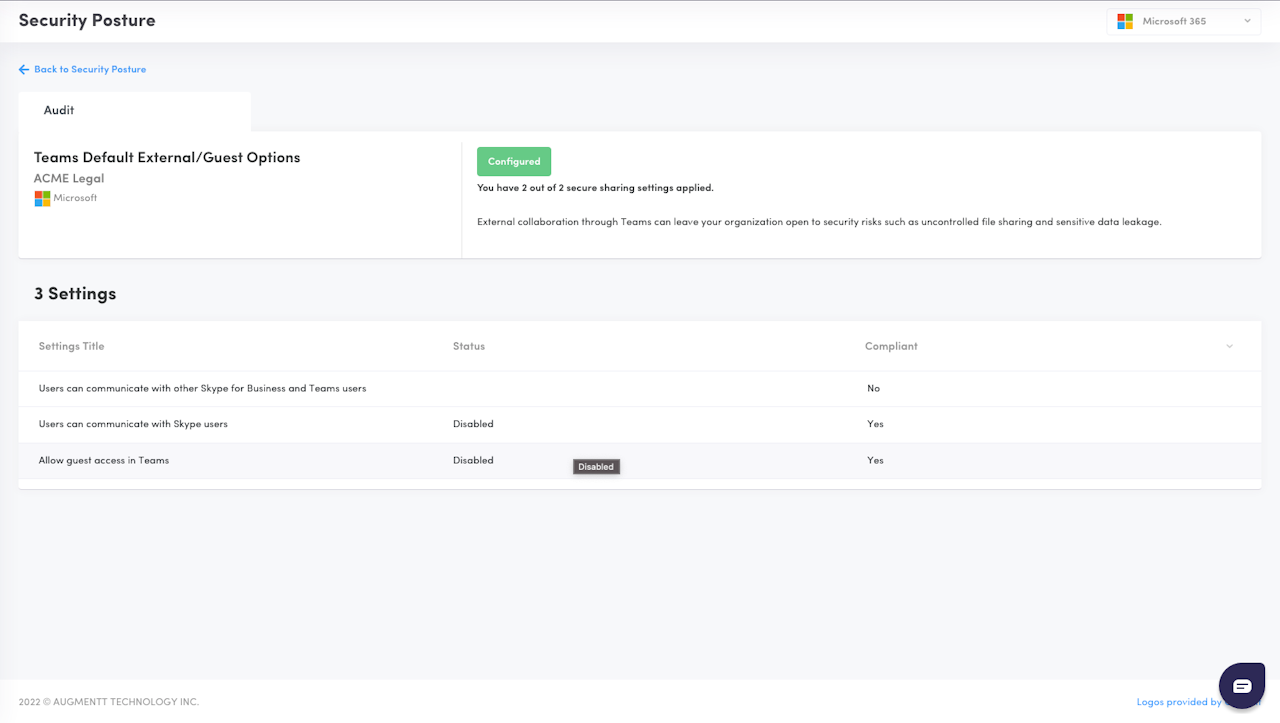
Teams Default External/Guest Options
Description: Verifies if Teams is configured to allow external communication by default on 3 settings:
“Users can communicate with other Skype for Business and Teams users” is compliant when set to "Disabled"
“Users can communicate with Skype users” is compliant when is set to "Disabled"
“Allow guest access in Teams” is compliant when is set to "Disabled"
Why: External collaboration through Teams can leave your organization open to security risks such as uncontrolled file sharing and sensitive data leakage. Employees should be making a conscious decision and assessing the risks when collaborating externally, rather than being the default.
Configured: All 3 settings are disabled by default; Scores 2 points
Partially Configured: At least 1 setting is disabled by default; Scores 1 point
Not Configured: None of the settings are disabled by default; Scores 0 points
Microsoft Licensing: Works with Basic licensing
Secure Score Impact: YES
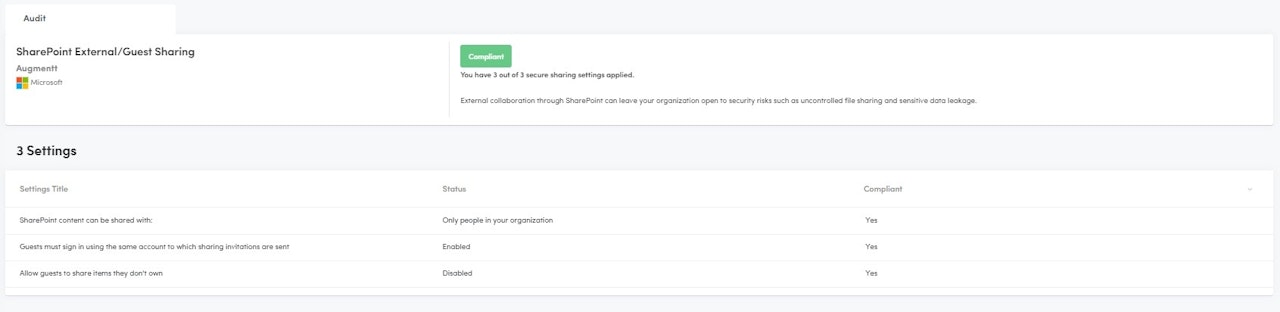
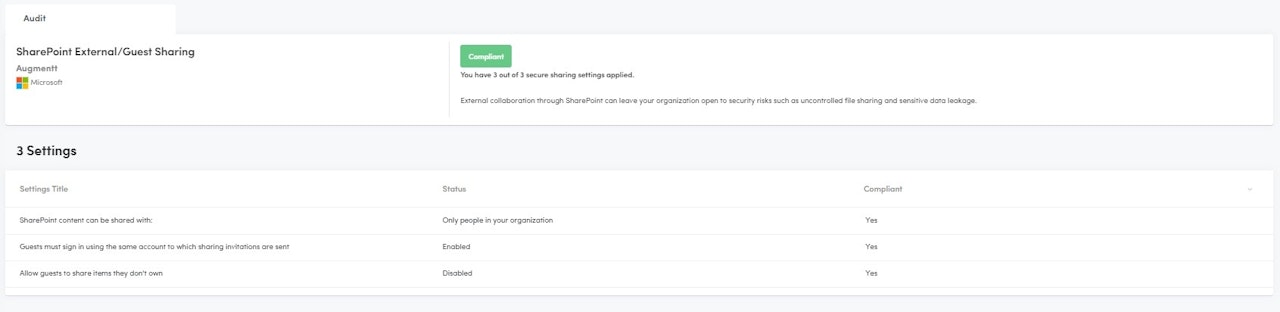
SharePoint External/Guest Sharing
Description: Verifies if SharePoint is configured to allow external collaboration by default on 3* settings:
“SharePoint content can be shared with” is considered compliant when it is not set to “Anyone” or "Only People in your organization"
“Guests must sign in using the same account to which sharing invitations are sent” is compliant when set to "Enabled"*
“Allow guests to share items they don’t own” is considered compliant when it is set to "Disabled"
Why: External collaboration through SharePoint can leave your organization open to security risks such as uncontrolled file sharing and sensitive data leakage. Employees should be making a conscious decision and assessing the risks when collaborating, rather than being the default.
Configured: All 3* settings are compliant; Scores 2 points
Partially Configured: At least 1 setting is compliant; Scores 1 point
Not Configured: None of the settings are compliant; Scores 0 points
Microsoft Licensing: Works with Basic licensing
Secure Score Impact: YES
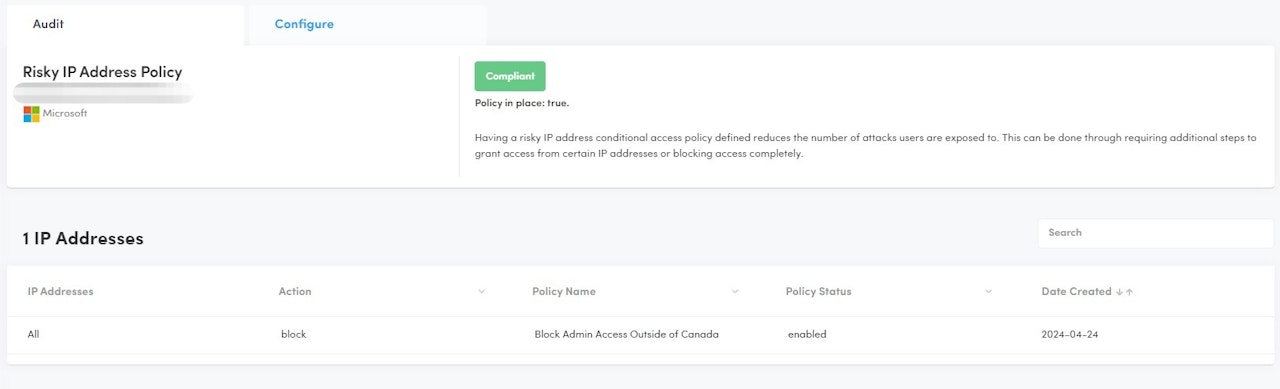
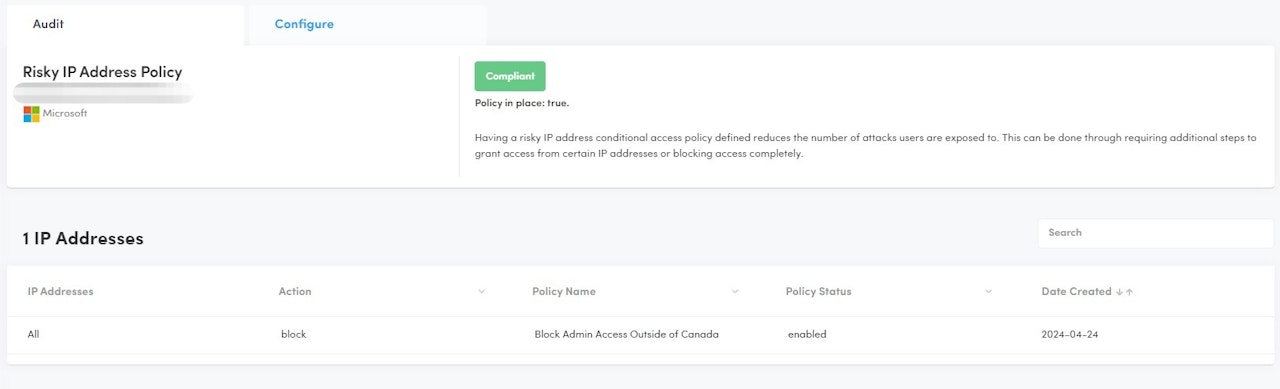
Risky IP Address Policy
Description: Verifies if a Conditional Access Policy is in place that blocks access based on IP address
Why: Having a risky IP address conditional access policy defined reduces the number of attacks users are exposed to. This can be done through requiring additional steps to grant access from certain IP addresses or blocking access completely.
Configured: A conditional access policy blocking access based on IP address exists; Scores 1 point
Make sure your Named Locations is set with Location Type: IP Ranges
Not Configured: A conditional access policy blocking access based on IP address does not exist; Scores 0 points
Microsoft Licensing: Requires Premium (P1) licensing
Secure Score Impact: YES
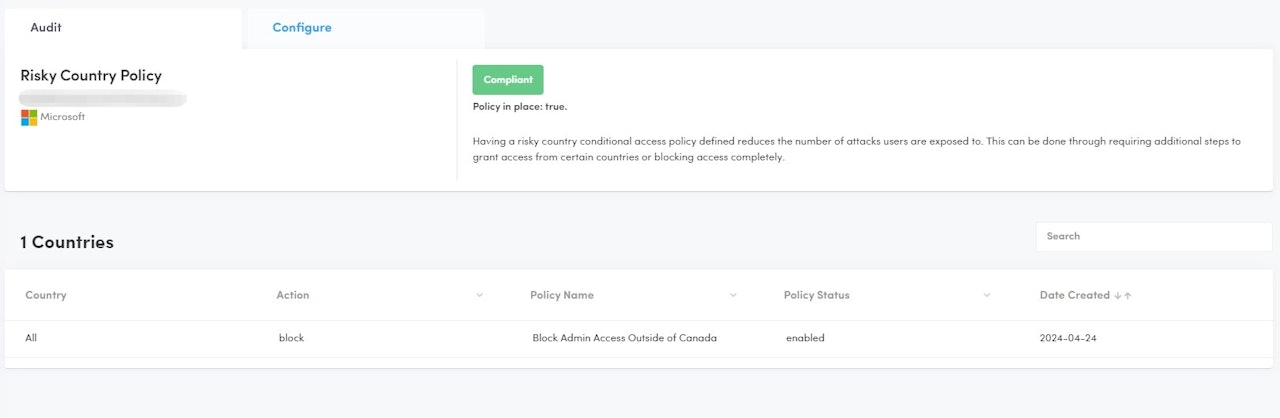
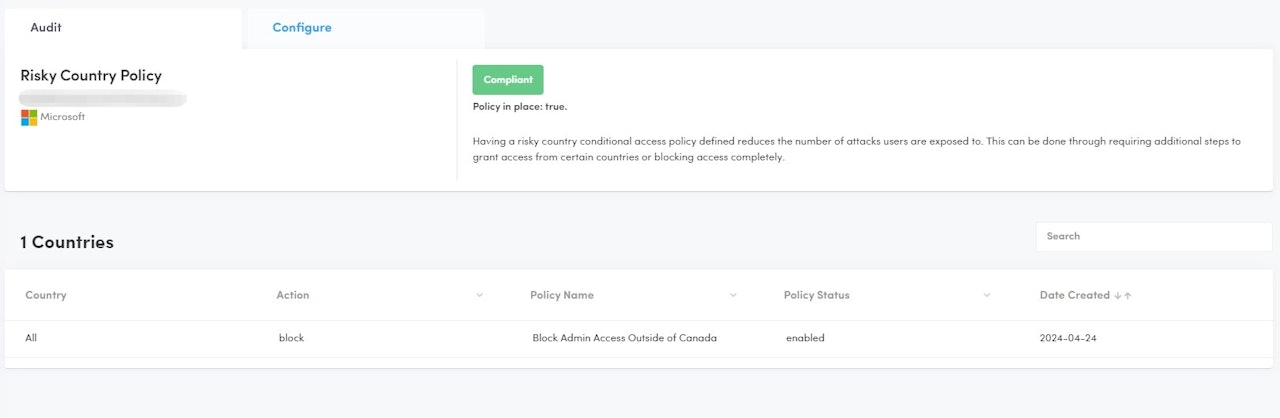
Risky Country Policy
Description: Verifies if a Conditional Access Policy is in place that blocks access based on Countries
Why: Having a risky country conditional access policy defined reduces the number of attacks users are exposed to. This can be done through requiring additional steps to grant access from certain countries or blocking access completely.
Configured: A conditional access policy blocking access based on Countries exists; Scores 1 point
Make sure your Named Locations is set with Location Type: Country(IP)
Not Configured: A conditional access policy blocking access based on Countries does not exist; Scores 0 points
Microsoft Licensing: Requires Premium (P1) licensing
Secure Score Impact: YES
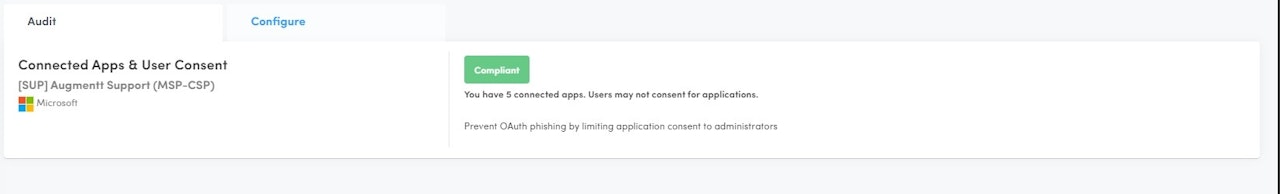
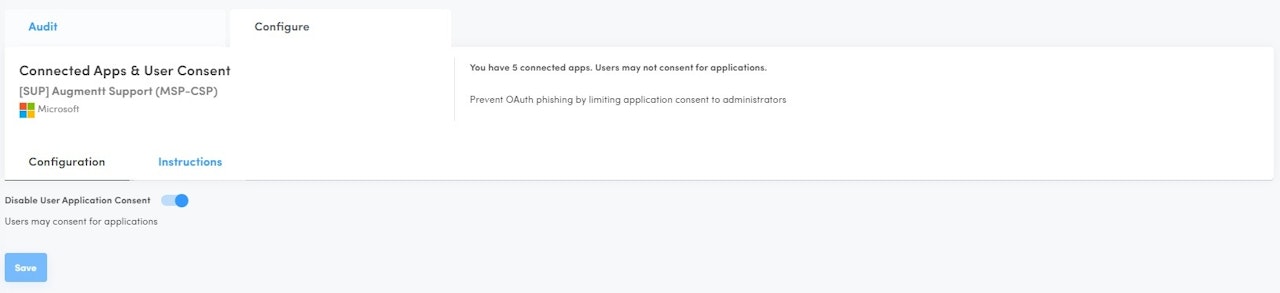
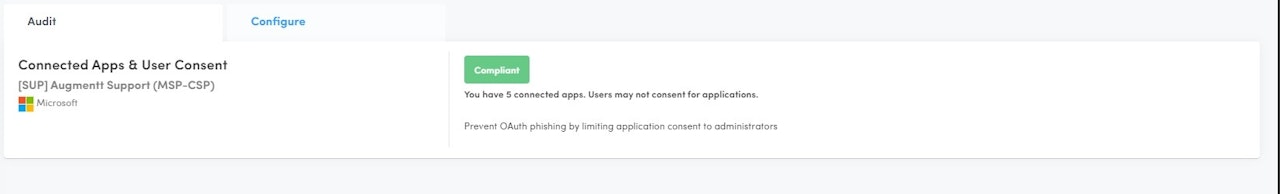
Connected Apps & User Consent
Description: Verifies if users can consent to application integrations in M365
Why: Users integrating applications in M365 without admin oversight can lead to vulnerabilities such as phishing and hacking.
Configured: Only admins can consent to applications; Scores 1 points
Not Configured: Users can consent to applications; Scores 0 points
Microsoft Licensing: Works with Basic licensing
Secure Score Impact: YES
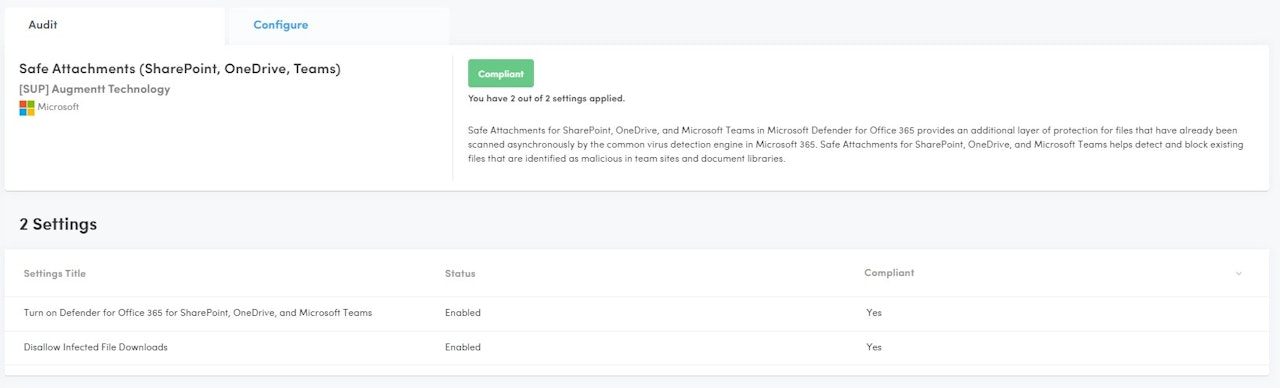
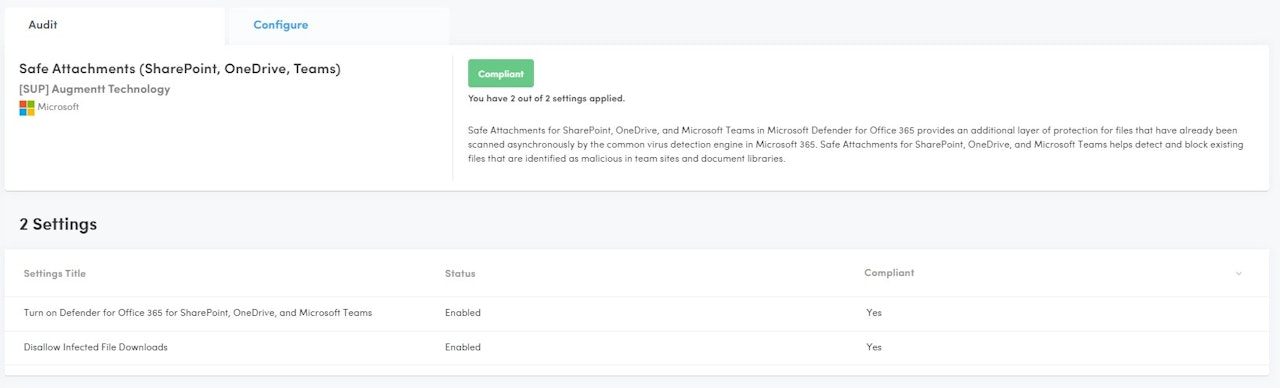
Safe Attachments
Description: Verifies that Defender for Office 365 and the option to disallow infected file downloads are enabled.
Why: Safe Attachments for SharePoint, OneDrive, and Microsoft Teams in Microsoft Defender for Office 365 provides an additional layer of protection for files that have already been scanned asynchronously by the common virus detection engine in Microsoft 365. Safe Attachments for SharePoint, OneDrive, and Microsoft Teams helps detect and block existing files that are identified as malicious in team sites and document libraries.
Configured: Both Settings are Enabled
Partially Configured: Defender for Office 365 is enabled but not the option to disallow infected file downloads
Not Configured: Defender for Office 365 is disabled
Microsoft Licensing: M365 Defender
Secure Score Impact: YES
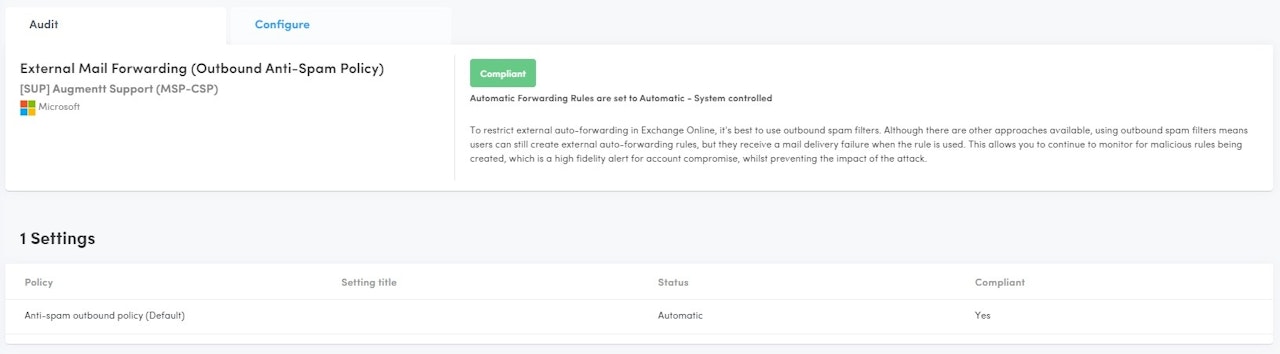
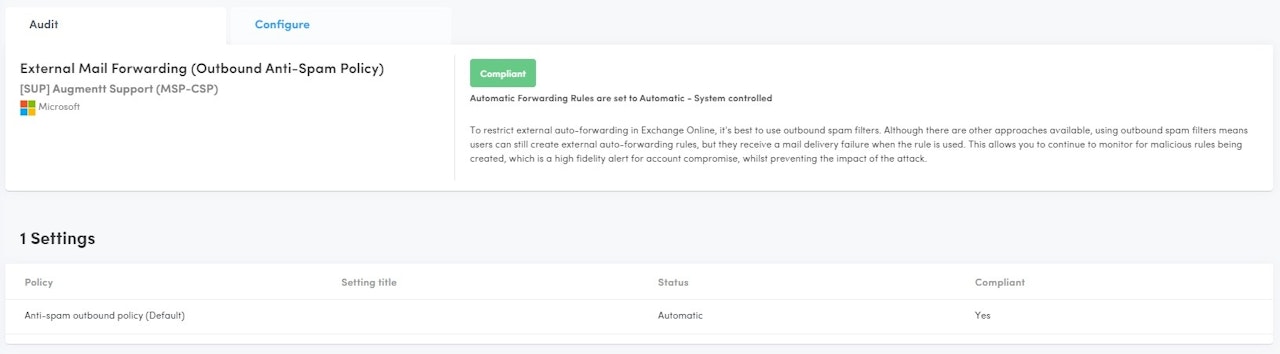
External Mail Forwarding
Description: Verifies that the outbound Anti-spam policies are configured to disable automatic forwarding rules.
Why: To restrict external auto-forwarding in Exchange Online, it's best to use outbound spam filters. Although there are other approaches available, using outbound spam filters means users can still create external auto-forwarding rules, but they receive a mail delivery failure when the rule is used. This allows you to continue to monitor for malicious rules being created, which is a high-fidelity alert for account compromise, whilst preventing the impact of the attack.
Configured: Forwarding is disabled
Not Configured: Forwarding is enabled
Microsoft Licensing: M365 Defender
Secure Score Impact: YES
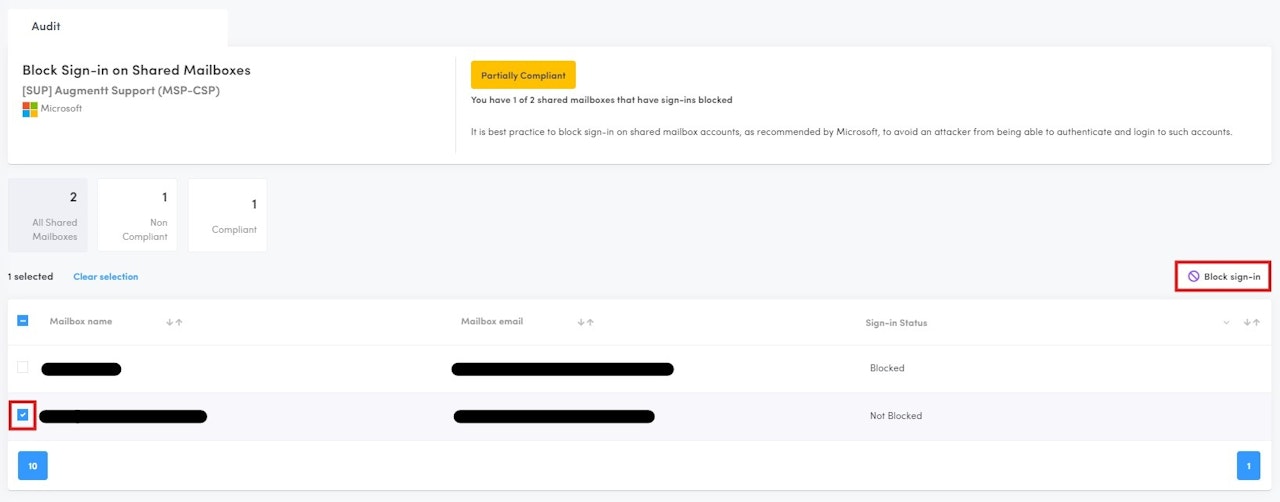
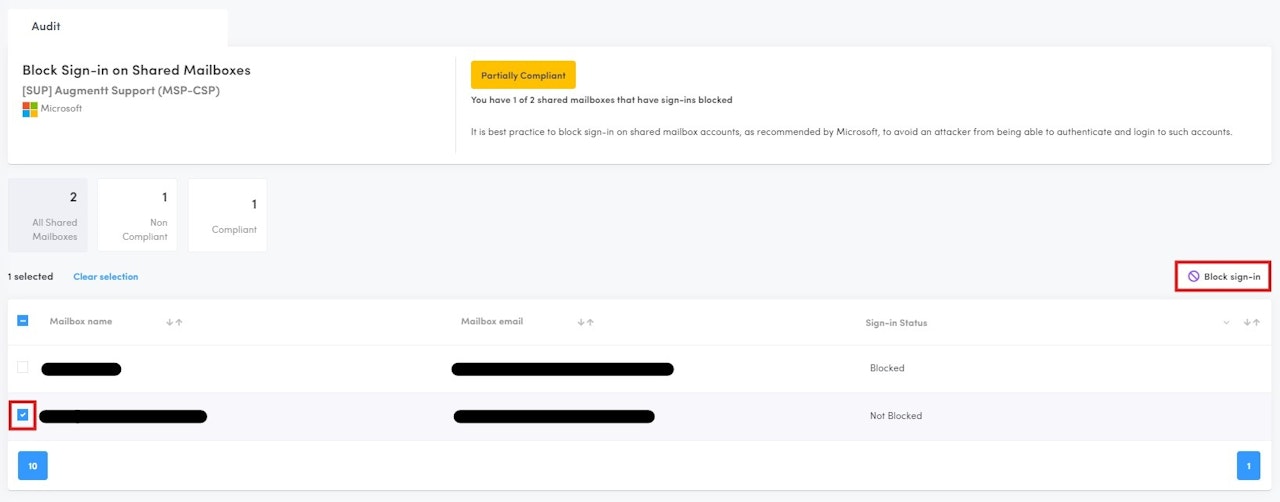
Block Sign-in on Shared Mailboxes
Description: Monitors for Shared Mailboxes that do not have logins disabled.
Why: As shared mailboxes are typically not monitored directly by a user, it is best practice to block sign-in on shared mailbox accounts, as recommended by Microsoft and the MSP community, to avoid an attacker from being able to authenticate and login to such accounts.
Configured: All Shared Mailbox accounts sign-in are blocked
Not Configured: 1 or more Shared Mailbox account(s) sign-in are not blocked
Microsoft Licensing: Works with Basic licensing
Secure Score Impact: No
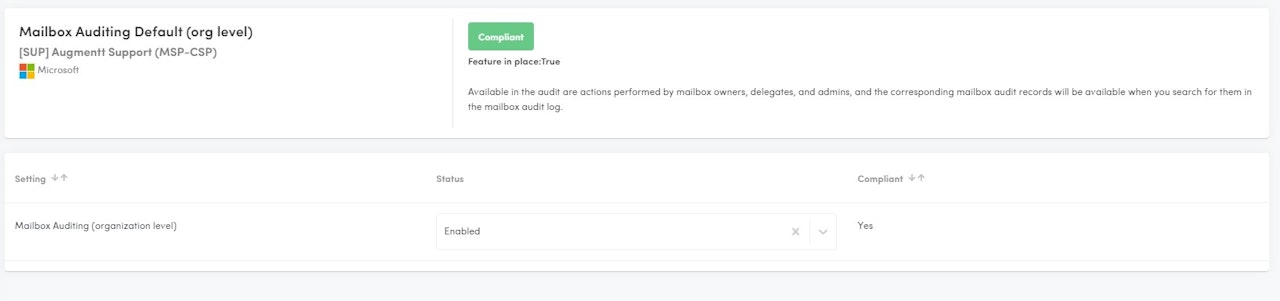
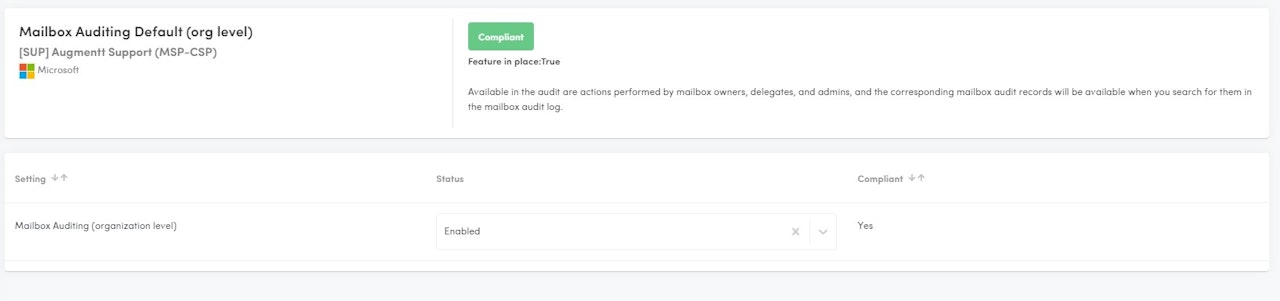
Mailbox Auditing Default (org level)
Description: Verifies that the Mailbox Auditing Default (org level) setting is enabled at the organization.
Why: Available in the audit are actions performed by mailbox owners, delegates, and admins, and the corresponding mailbox audit records will be available when you search for them in the mailbox audit log.
Configured: Mailbox auditing is enabled.
Not Configured: Mailbox auditing is disabled.
Microsoft Licensing: Works with Basic licensing
Secure Score Impact: YES
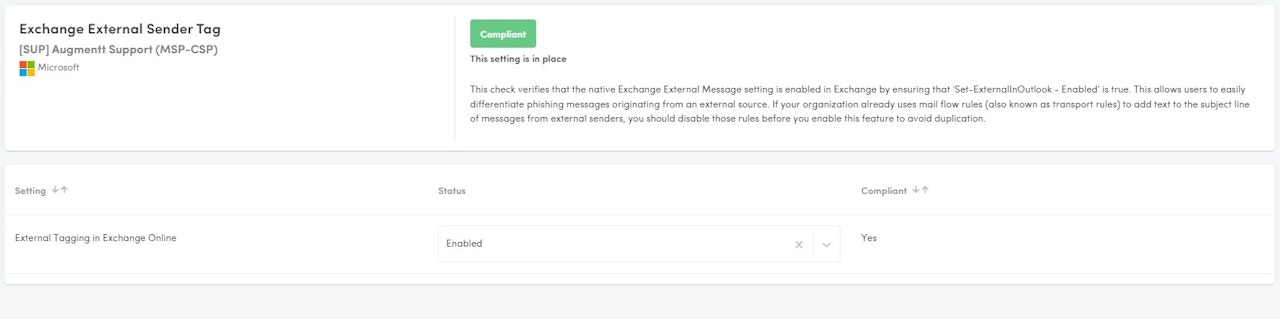
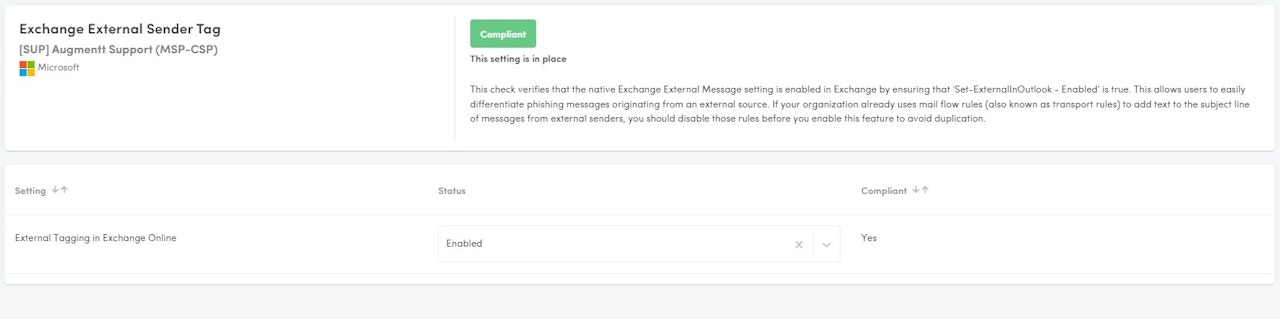
Exchange External Sender Tag
Description: This check verifies that the native Exchange External Message setting is enabled in Exchange by ensuring that 'Set-ExternalInOutlook - Enabled' is true.
Why: This allows users to easily differentiate phishing messages originating from an external source. If your organization already uses mail flow rules (also known as transport rules) to add text to the subject line of messages from external senders, you should disable those rules before you enable this feature to avoid duplication.
Security Awareness: The tag alerts users that an email originated from an external sender (someone outside the organization). It encourages caution and prompts recipients to double-check the email’s legitimacy. Even with robust spam filters, user awareness remains essential in preventing spyware and malicious links.
Phishing Prevention: Despite measures like SPF, DKIM, and DMARC, some phishing and spam emails can still slip through. The external tag helps users identify potentially harmful messages and avoid clicking on suspicious links or attachments.
Visual Cue: When an email bears the “External” tag, it stands out visually. Users can quickly recognize that the sender is not part of their organization, prompting them to exercise caution.
Admin Tracking: For administrators, external tags assist in tracking and monitoring potentially risky emails. It helps identify patterns and assess security threats.
Cofiguration Settings
Configured: Exchange External Sender Tag is enabled.
Not Configured: Exchange External Sender Tag is disabled.
Microsoft Licensing: Works with Basic licensing
Secure Score Impact: No
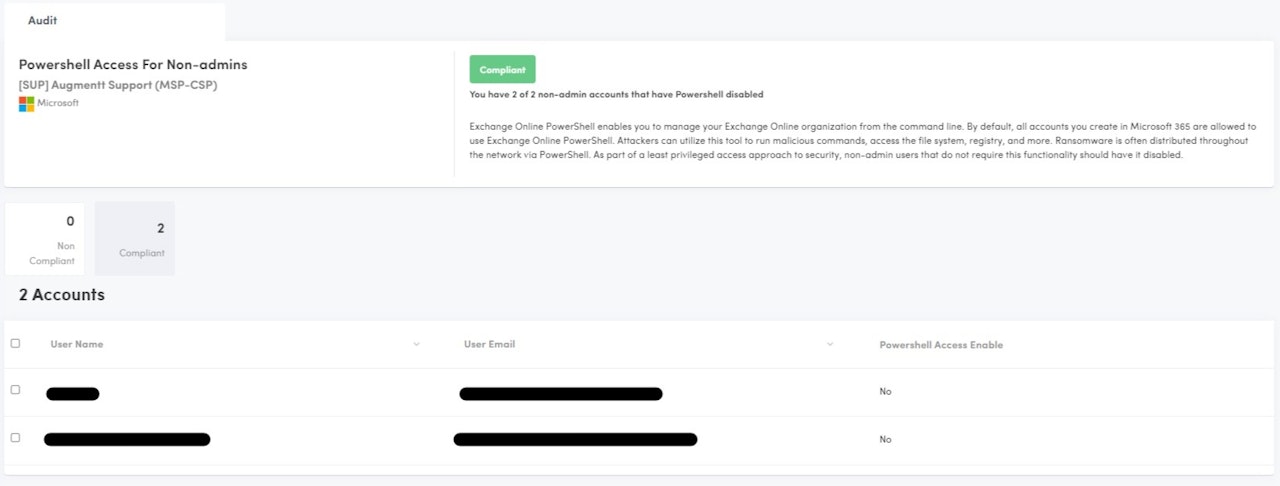
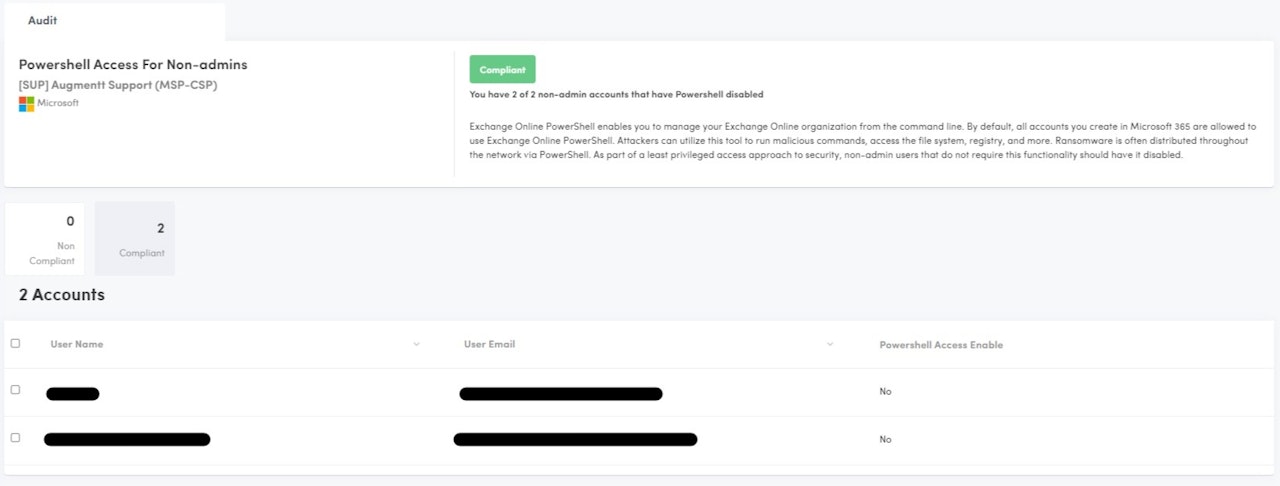
Powershell Access for Non-Admins
Description: This check verifies that end users cannot run powershell against the M365 organization.
Why: Exchange Online PowerShell enables you to manage your Exchange Online organization from the command line. By default, all accounts you create in Microsoft 365 are allowed to use Exchange Online PowerShell. Attackers can utilize this tool to run malicious commands, access the file system, registry, and more. Ransomware is often distributed throughout the network via PowerShell. As part of a least privileged access approach to security, non-admin users that do not require this functionality should have it disabled.
Configured: All non-admin users do not have the ability to execute Powershell against the M365 organization.
Not Configured: 1 or more non-admin users have the ability to execute Powershell against the M365 organization.
Microsoft Licensing: Works with Basic licensing
Secure Score Impact: No
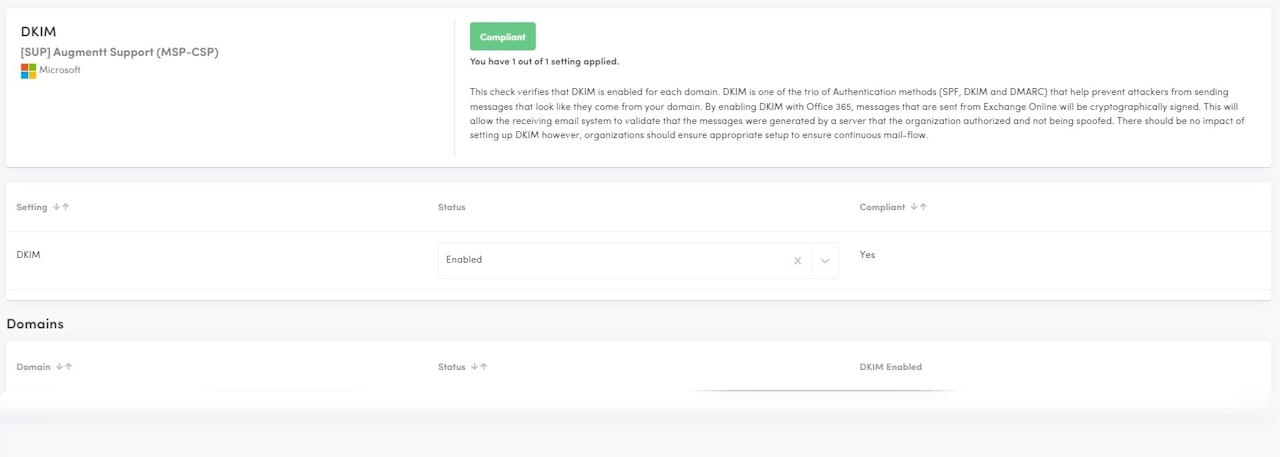
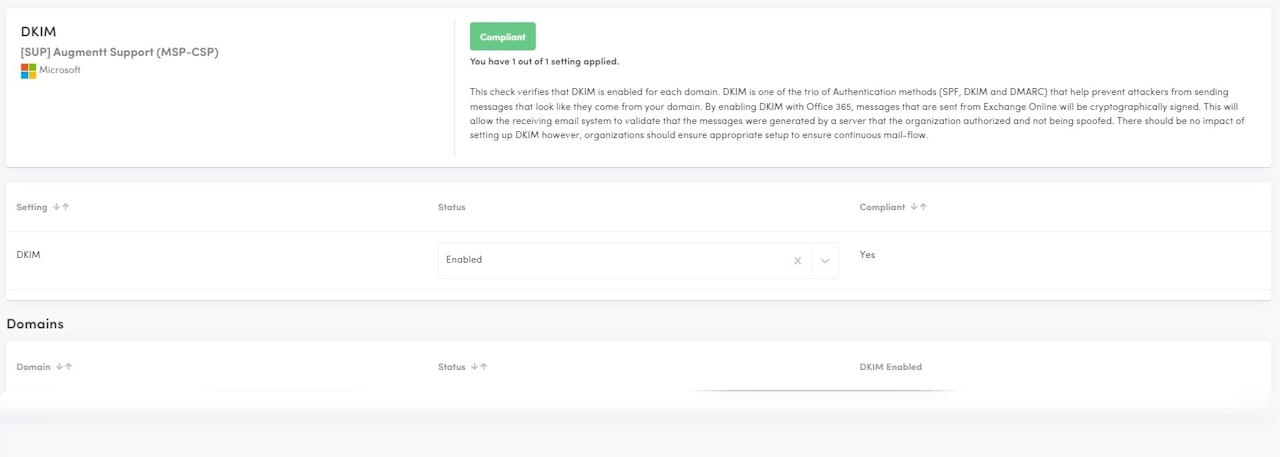
DKIM
Description: This check verifies that DKIM is enabled for each domain.
Why: DKIM is one of the trio of Authentication methods (SPF, DKIM and DMARC) that help prevent attackers from sending messages that look like they come from your domain. By enabling DKIM with Office 365, messages that are sent from Exchange Online will be cryptographically signed. This will allow the receiving email system to validate that the messages were generated by a server that the organization authorized and not being spoofed. There should be no impact of setting up DKIM however, organizations should ensure appropriate setup to ensure continuous mail-flow.
Configured: All domains have DKIM configured.
Not Configured: 1 or more domains does not have DKIM configured.
Microsoft Licensing: Works with Basic licensing
Secure Score Impact: No
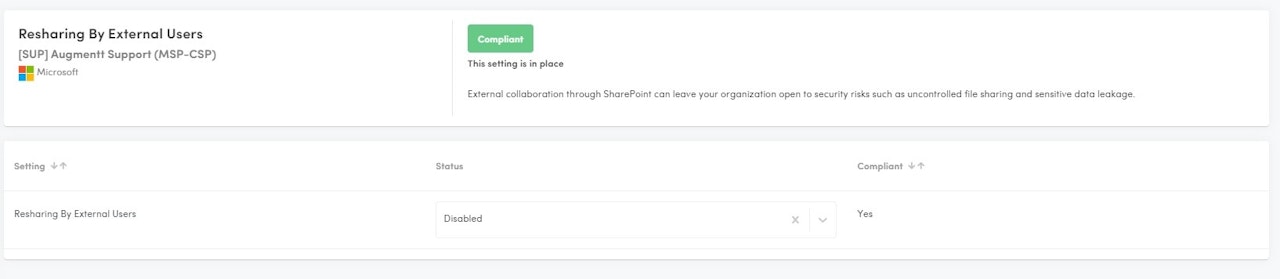
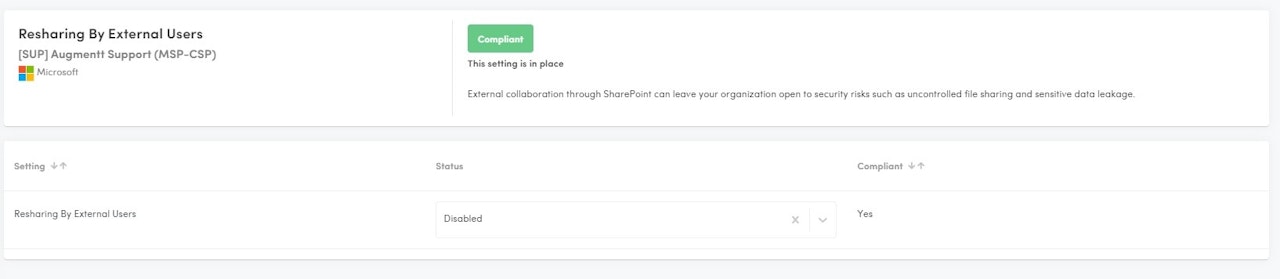
Resharing by External Users
Description: This check verifies that Resharing of files by External Users is disabled.
Why: External collaboration through SharePoint can leave your organization open to security risks such as uncontrolled file sharing and sensitive data leakage.
Configured: Resharing by External users is disabled.
Not Configured: Resharing by External users is enabled.
Microsoft Licensing: Works with Basic licensing
Secure Score Impact: No
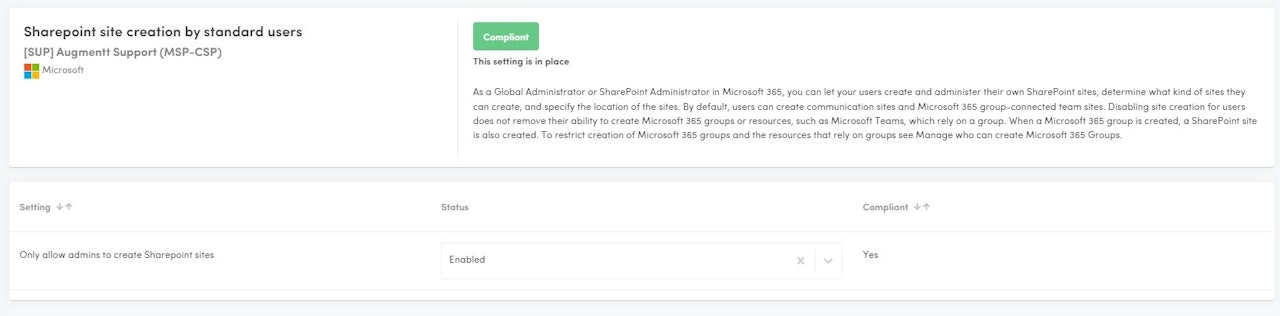
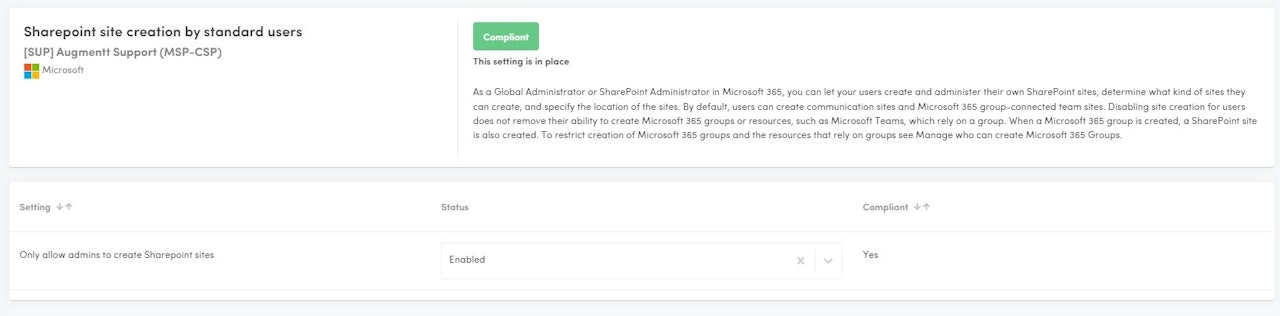
Sharepoint Site Creation by Standard Users
Description: This check verifies if Sharepoint sites could be created by standard users.
Why: As a Global Administrator or SharePoint Administrator in Microsoft 365, you can let your users create and administer their own SharePoint sites, determine what kind of sites they can create, and specify the location of the sites. By default, users can create communication sites and Microsoft 365 group-connected team sites. Disabling site creation for users does not remove their ability to create Microsoft 365 groups or resources, such as Microsoft Teams, which rely on a group. When a Microsoft 365 group is created, a SharePoint site is also created. To restrict creation of Microsoft 365 groups and the resources that rely on groups see Manage who can create Microsoft 365 Groups.
Configured: Users cannot create Sharepoint sites.
Not Configured: Users can create Sharepoint sites.
Microsoft Licensing: Works with Basic licensing
Secure Score Impact: No
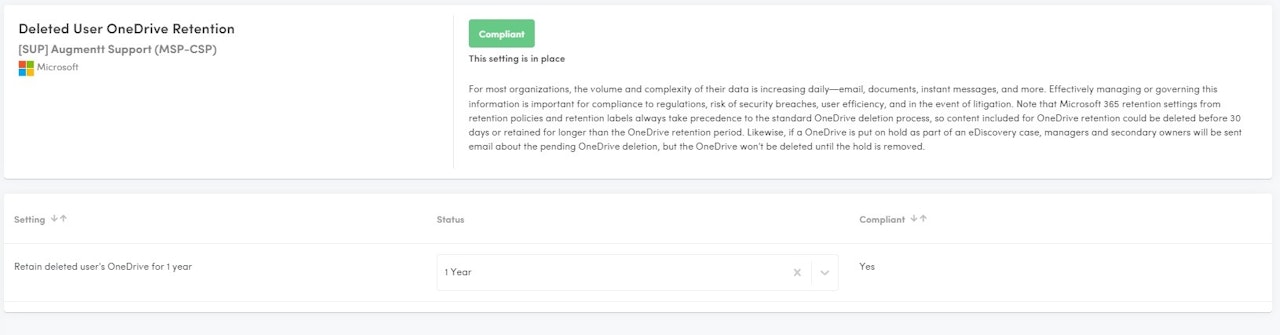
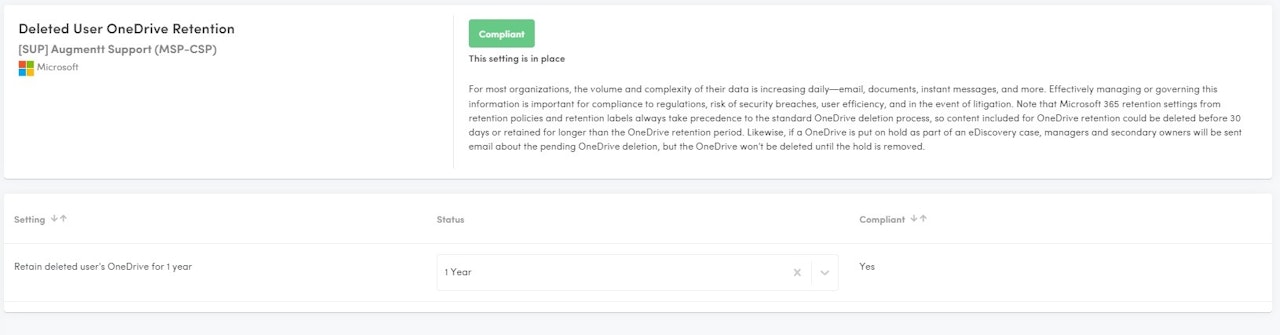
Deleted Users OneDrive Retention
Description: This check verifies that Deleted User's OneDrive Retention settings are extended to 1 year.
Why: For most organizations, the volume and complexity of their data is increasing daily—email, documents, instant messages, and more. Effectively managing or governing this information is important for compliance to regulations, risk of security breaches, user efficiency, and in the event of litigation. Note that Microsoft 365 retention settings from retention policies and retention labels always take precedence to the standard OneDrive deletion process, so content included for OneDrive retention could be deleted before 30 days or retained for longer than the OneDrive retention period. Likewise, if a OneDrive is put on hold as part of an eDiscovery case, managers and secondary owners will be sent email about the pending OneDrive deletion, but the OneDrive won't be deleted until the hold is removed.
Configured: Deleted user's OneDrive is retained for 1 year.
Not Configured: Deleted User's OneDrive is retained for less than 1 year.
Microsoft Licensing: Works with Basic licensing
Secure Score Impact: No
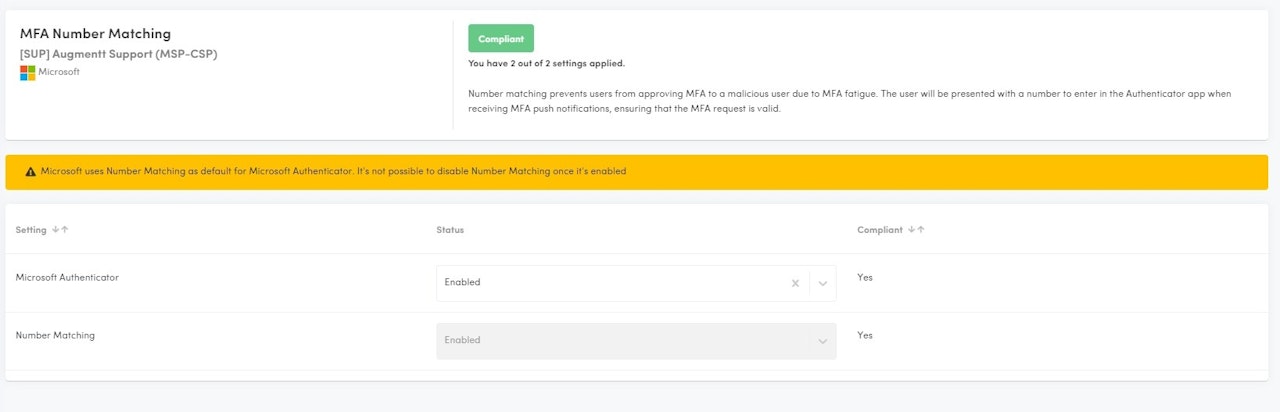
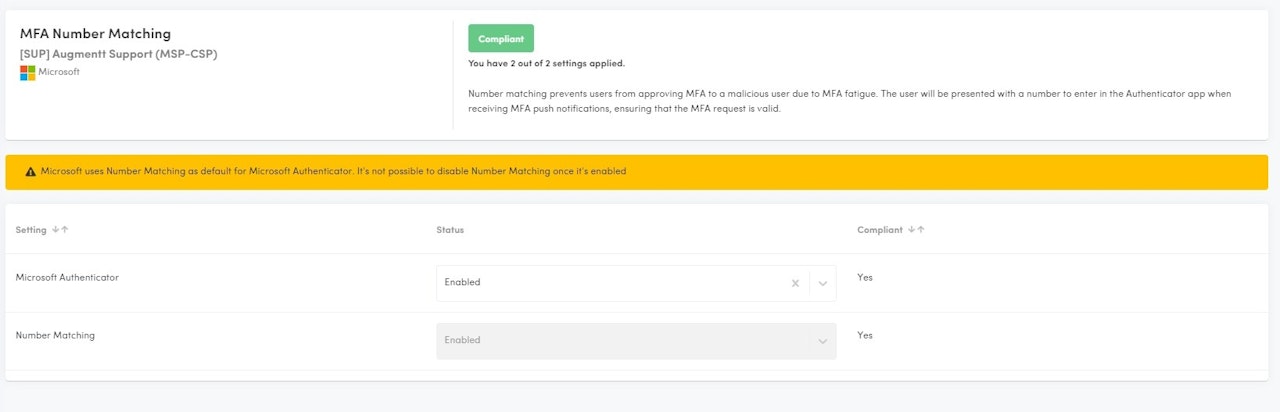
MFA Number Matching
Description: This check verifies that MFA Number Matching is enabled. This requires the Microsoft Authenticator app to be enabled/used.
Why: Number matching prevents users from approving MFA to a malicious user due to MFA fatigue. The user will be presented with a number to enter in the Authenticator app when receiving MFA push notifications, ensuring that the MFA request is valid.
Configured: Number matching is enabled.
Not Configured: Number matching is disabled.
Microsoft Licensing: Works with Basic licensing
Secure Score Impact: No
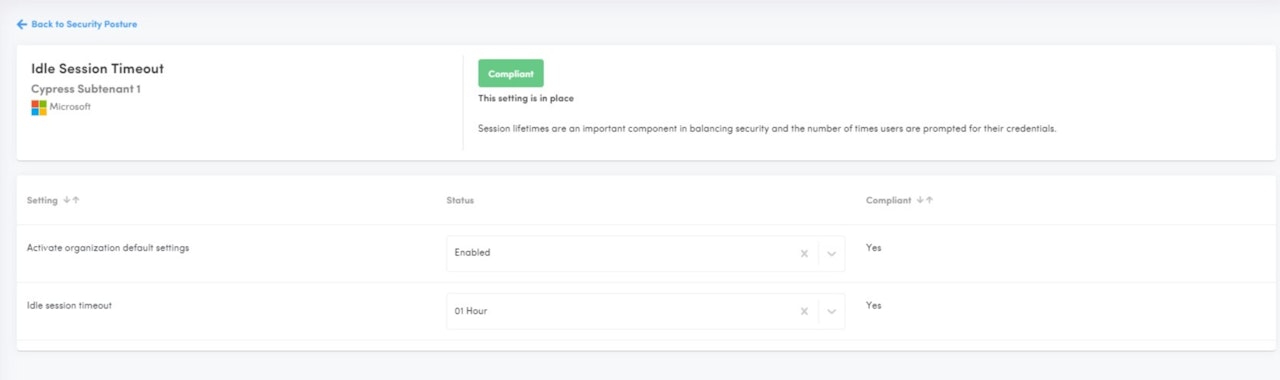
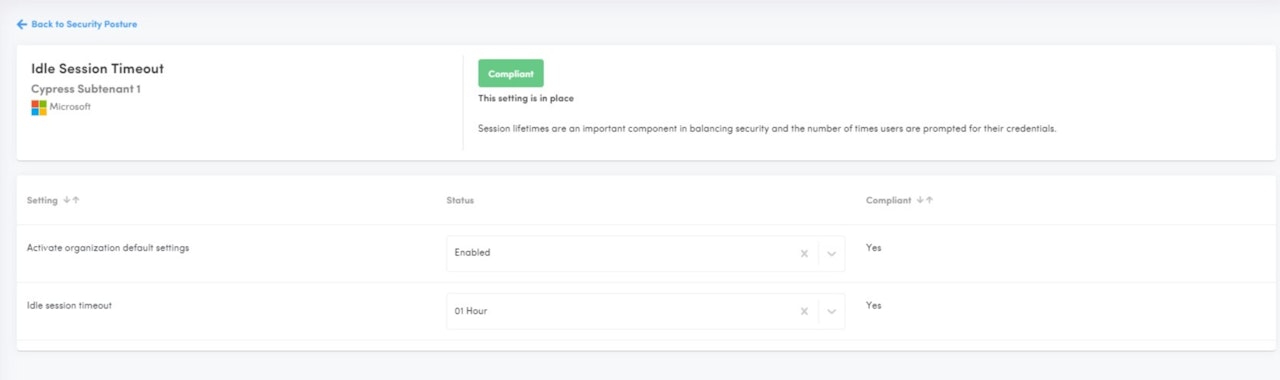
Idle Session Timeout
Description: Idle session timeout automatically signs out users from Microsoft 365 web apps after a set period of inactivity.
Why Use It?
Enhanced Security: Reduces the risk of unauthorized access to data.
Data Protection: Safeguards sensitive information when a device is left unattended.
Compliance: Helps meet regulatory requirements for session management.
Mitigates Risks: Lowers the chance of session hijacking.
Microsoft Licensing: Works with Basic licensing
Secure Score Impact: YES
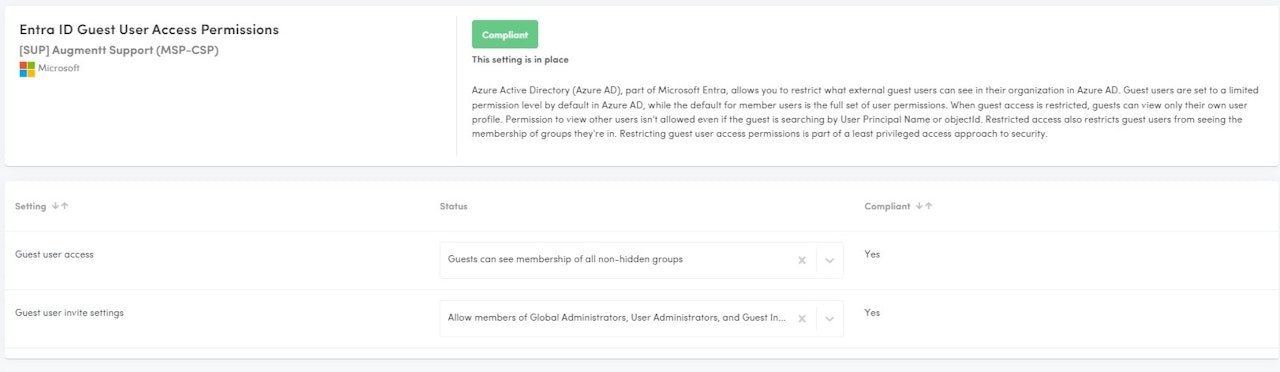
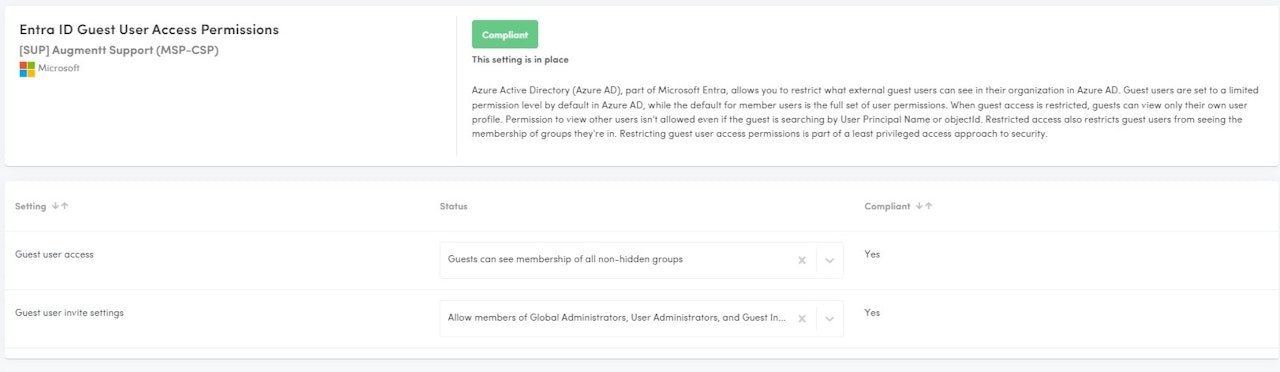
Entra ID Guest User Access Permissions
Description: Guest user access permissions in Entra ID manage what external users can access within your organization’s resources. This feature helps control the level of access granted to guests, ensuring that they have the necessary permissions without compromising security.
Why Use It?
Boost Security: Limits guest access to protect sensitive data.
Ensure Compliance: Meets regulatory and organizational standards.
Manage Access: Tailors permissions to fit collaboration needs.
How to be Compliant?
Guest user access, select either:
Guests can see membership of all non-hidden groups
Guests can't see membership of any groups
Guest user invite settings, select either:
Prevent everyone, including admins, from inviting external users.
Allow members of Global Administrators, User Administrators, and Guest Inviter roles to invite external users.
Microsoft Licensing: Works with Basic licensing
Secure Score Impact: No
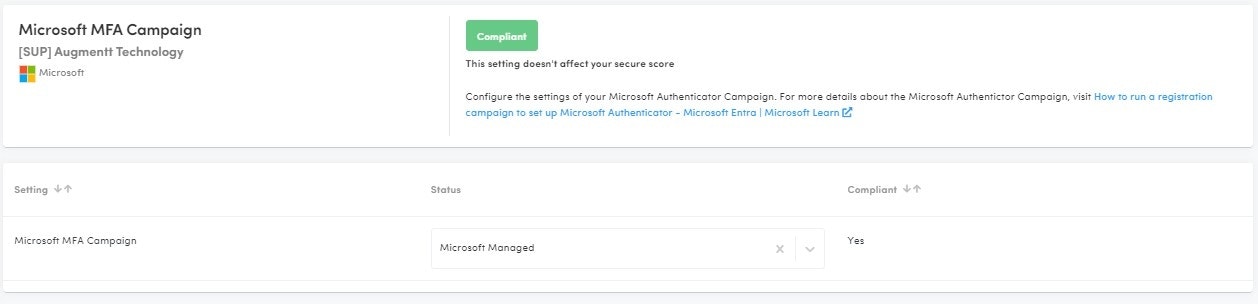
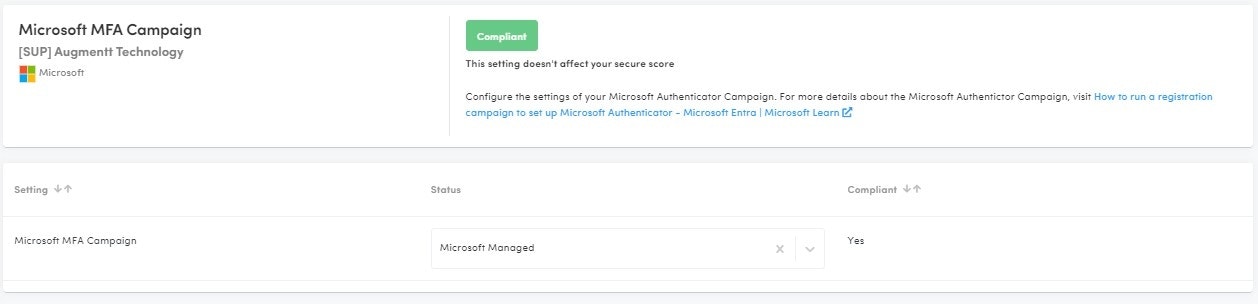
Microsoft MFA Campaign
Description: A registration campaign in Microsoft Azure AD is a feature that enables administrators to encourage or require users to register for Azure Multi-Factor Authentication (MFA) and self-service password reset (SSPR) in a phased rollout, allowing for a gradual transition to more secure authentication methods.
Why: This campaign enables administrators to specify which users are prompted to register, customize the registration experience, and set a deadline for registration, ensuring that users are adequately prepared and informed throughout the process.
Compliant: Enabled or Microsoft Managed
Not Compliant: Disabled
Microsoft Licensing: Works with Basic licensing
Secure Score Impact: No
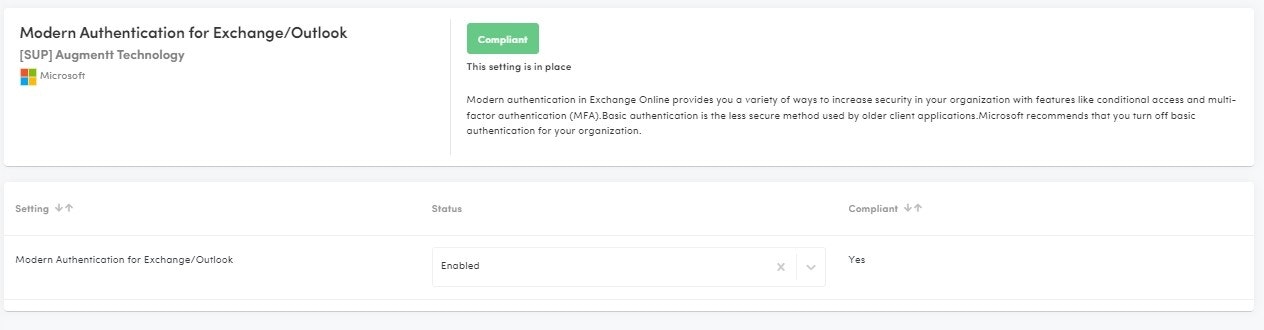
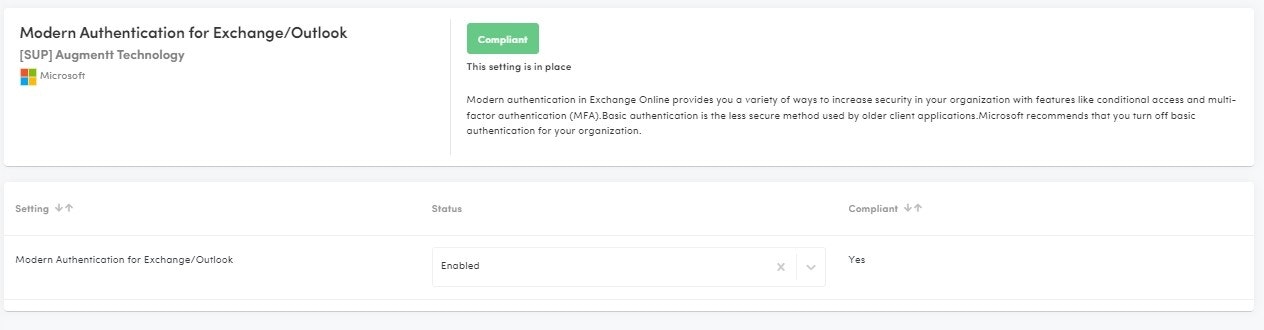
Modern Authentication for Exchange/Outlook
Description: Modern authentication in Exchange Online provides you with a variety of ways to increase security in your organization with features like conditional access and multi-factor authentication (MFA).
Why: Basic authentication is the less secure method used by older client applications. Microsoft recommends that you turn off basic authentication for your organization.
Microsoft Licensing: Works with Basic licensing
Secure Score Impact: YES
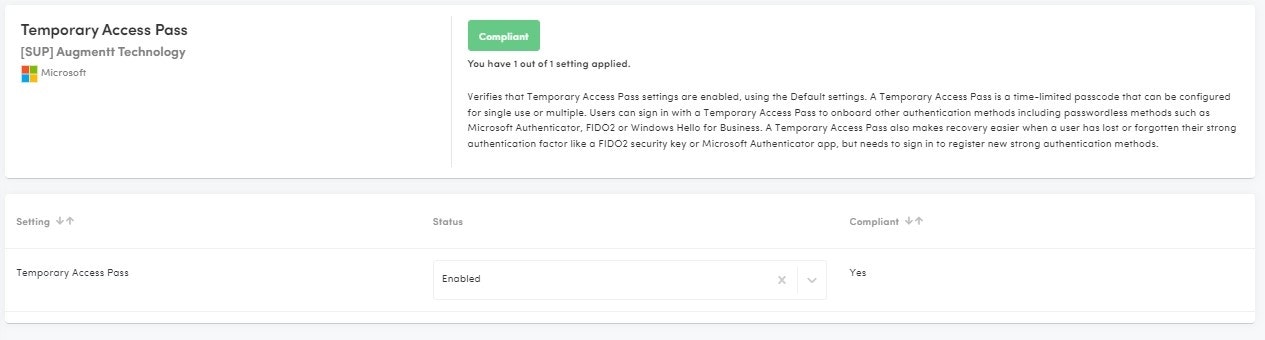
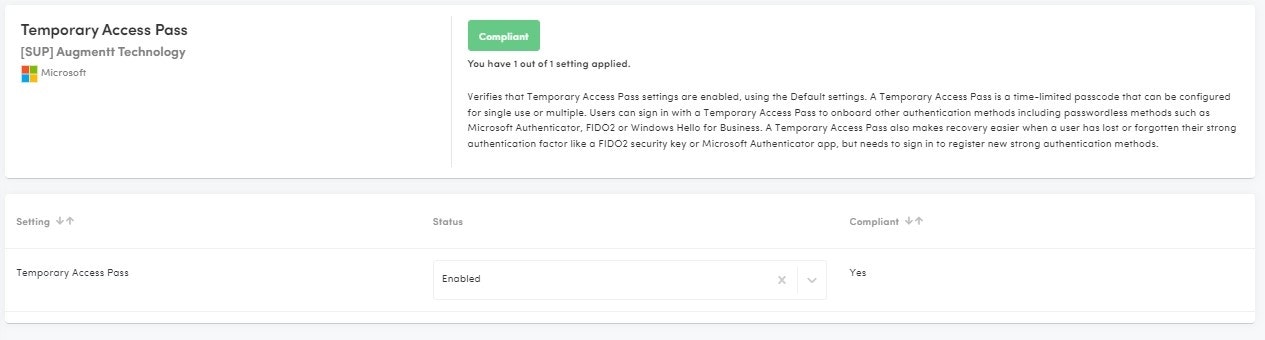
Temporary Access Pass
Description: This posture check verifies that Temporary Access Pass settings are enabled, using the Default settings.
Why: A Temporary Access Pass is a time-limited passcode that can be configured for single use or multiple. Users can sign in with a Temporary Access Pass to onboard other authentication methods including passwordless methods such as Microsoft Authenticator, FIDO2 or Windows Hello for Business. A Temporary Access Pass also makes recovery easier when a user has lost or forgotten their strong authentication factor like a FIDO2 security key or Microsoft Authenticator app, but needs to sign in to register new strong authentication methods.
Microsoft Licensing: Works with Basic licensing
Secure Score Impact: No
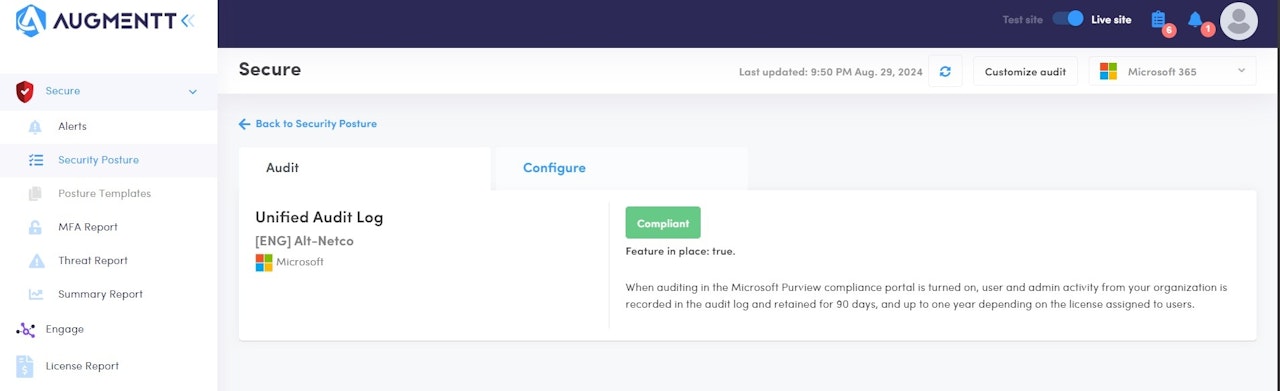
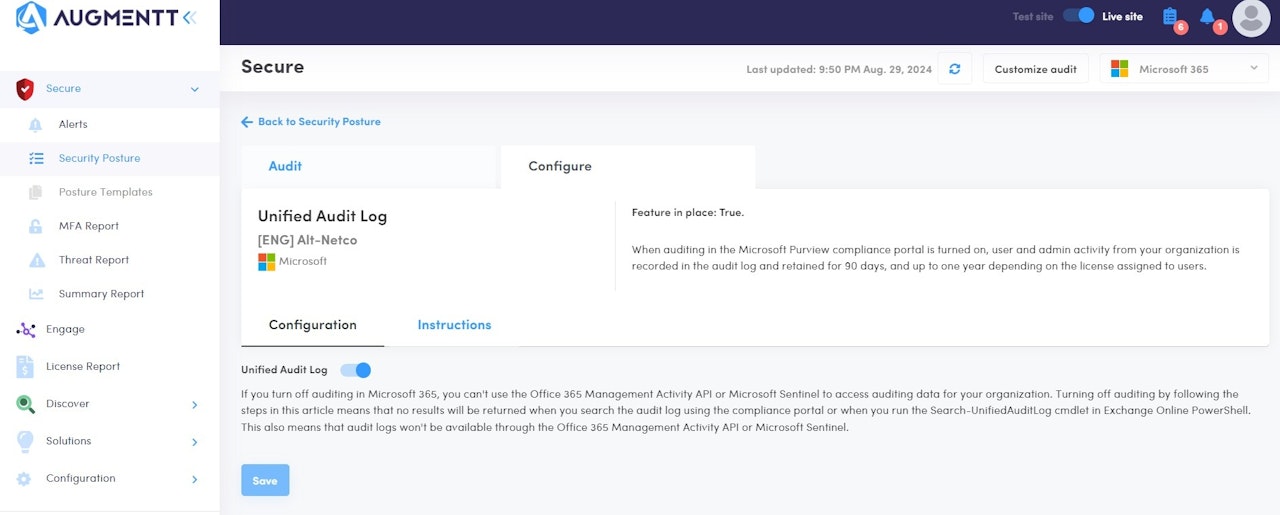
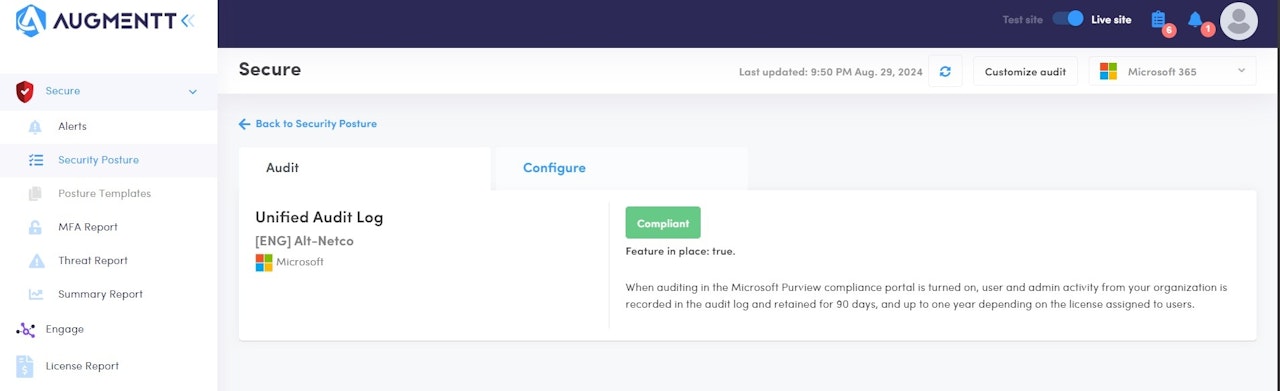
Unified Audit Log
Description: When auditing in the Microsoft Purview compliance portal is turned on, user and admin activity from your organization is recorded in the audit log and retained for 90 days, and up to one year depending on the license assigned to users.
Why: Unified Audit Logs in Microsoft Purview provide a centralized and comprehensive record of user and administrative activities across Microsoft 365 services, capturing thousands of operations daily. This centralized logging is crucial for security as it enables organizations to monitor, investigate, and respond to potential security incidents effectively. By retaining detailed logs of activities, organizations can conduct forensic investigations to determine the scope of a compromise, identify malicious actions, and ensure compliance with regulatory requirements. The ability to search and analyze these logs helps in detecting anomalies, understanding user behavior, and enhancing overall security posture by providing visibility into actions that could indicate security threats
Microsoft Licensing: Works with Basic licensing
Secure Score Impact: YES